CEH Training in Hyderabad - C|EHv12
(Certified Ethical Hacker) Course
Course Fees: INR 15,000/-
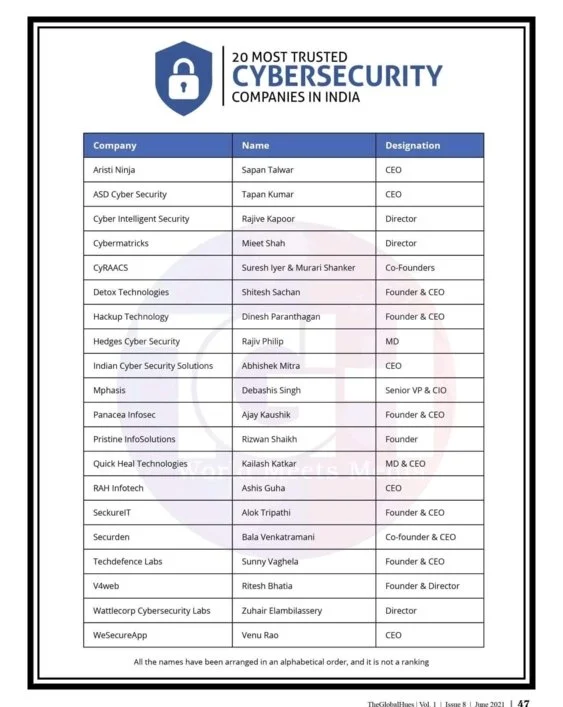
CEH Training in Hyderabad by Indian Cyber Security Solutions upgrades your preparation. We stand out by providing special tips for the exam and careful guidance on various question types. Your readiness gets a boost, making sure you're not just prepared but all set for success. We have a pool of certified ethical hackers who are employed as security analysts by various companies. CEH Training in Hyderabad ensures global recognition, spanning over 160 countries with its certification validity.
A group of skilled specialists with experience that goes beyond the realms of theory make up the core of Indian Cyber Security Solutions. This skill set not only improves your professional standing but also equips your company to proactively address security issues. You have access to a cohort that not only teaches cybersecurity, but also practices it on a global scale thanks to the roster of over 130 trainers, each of whom is an expert in ethical hacking. These knowledgeable instructors are not only excellent teachers but also significant members of our vibrant development team. ICSS is actively involved in cybersecurity research and development, staying at the forefront of technological advancements. This commitment to innovation ensures that training content is up-to-date and relevant. Begin your powerful adventure by joining us at Indian Cyber Security Solutions right away!
Enroll for
Online Live Class
Get Started with FREE Demo Class
Note: "Certified Ethical Hacker" and "CEH" is a registered trademarks of EC-Council and this course is not licensed, endorsed, or affiliated with EC-Council in any way.
UNIVERSITY TRAINING PARTNER'S
Key Highlights
No Cost EMI & Educational Loan
100% Placement Support
3 Months Training
Classroom Training
Online Training
Program Duration
3 Months
Get First 2 Classes FREE
Enroll Now !!
Please contact us using the form below
No Advance Payment Required
Learning Format
Why Join CEH Training at ICSS
Reviews
4.8
1,09,233
Students Enrolled in
Indian Cyber Security Solutions

Reviews
4.8
CEH Course in Hyderabad
Enhance Your Tech Skill Set
CEH Course in Hyderabad, offered by ICSS, is designed to provide prospective cybersecurity professionals with a thorough understanding of ethical hacking methods. Organizations employ ethical hackers to infiltrate computer networks and systems to identify and patch security flaws.
This exam preparation training is highly beneficial for those planning to work in the cybersecurity sector. Cybersecurity experts at Indian Cyber Security Solutions, working as penetration testers, offer CEH courses in Hyderabad. Topics covered include DDoS attacks, social engineering, policy creation, and intrusion detection.
The extended exam preparation CEH course in Hyderabad focuses on 20 popular security fields, offering a practical approach to fundamental security systems. Utilizing penetration testing techniques, participants learn to assess computer system security. The course also provides firsthand exposure to sniffing, phishing, and exploitation techniques.
CEH training is in high demand, with major corporations such as TCS, ITC, and CTS actively seeking employees with CEH certification. In this industry, you can find the desired position, as ethical hackers are renowned in all information technology fields for their work as information security specialists. Organizations with crucial business data online often hire ethical hackers.
Best CEH Training Institute in Hyderabad
Optimal Choice for CEH Training
Best CEH Training Institute in Hyderabad, Indian Cyber Security Solutions, provides comprehensive exam preparation training to enhance your understanding of the tools and methods employed by hackers. As more businesses worldwide recognize the critical importance of maintaining robust cybersecurity measures, there is an increasing demand for certified ethical hackers.
Learners will gain practical experience and the confidence to handle challenging security issues through our experienced instructors, industry-relevant curriculum, and hands-on training methodology. Assistance continues even after your training is complete. Beyond certification, ICSS believes in developing students. Our post-training support equips you with the skills to handle real-world situations.
With the Best CEH Training Institute in Hyderabad, you can invest in your professional development now and open the door to a lucrative career in information security. For individuals aspiring to secure jobs in the information security industry, the CEH certification—recognized and sought after by leading companies—is an essential requirement.
When you choose ICSS, you are not just selecting a CEH exam preparation training facility; you are choosing a path to success in the dynamic field of cybersecurity. Join us, and together, we can defend the digital environment from threats.
Eligibility Criteria
Technical Background
Build on your technical foundation with CEH exam preparation training.
Non-Technical Background
Students from non-technical disciplines can also CEH exam preparation training.
CEH Certification in Hyderabad
Hack-Proof Your Future with CEH Certification
CEH Certification in Hyderabad unlocks pathways to a flourishing career in cybersecurity, especially as cybercriminals pose significant threats in the modern digital age. A few years ago, hackers received minimal attention, but today, Indian Cyber Security Solutions proudly stands as the top-rated CEH exam preparation training institute in Hyderabad, attracting over 1890 students worldwide each year.
Throughout our CEH exam preparation training, practical sessions enhance your skills, offering diverse opportunities in the information technology sector. Ethical hackers are esteemed for their roles as information security specialists. CEH certification is in high demand, with companies of all sizes seeking cybersecurity professionals to avert data breaches. Aspiring individual students pursuing CEH Certification can anticipate a minimum salary package of 3.0 Lakhs as entry-level professionals globally. This means your skills are acknowledged not only locally but on an international level, opening doors to a wide range of career opportunities.
Holding a CEH certification can significantly boost your career. Employers often prefer or require certified professionals for cybersecurity roles, and having CEH on your resume can lead to promotions and higher salary offers. It's an investment in your professional growth. Seize the opportunity to become a certified ethical hacker. Enroll today for top-notch CEH exam preparation training and unlock a world of career possibilities!
Get Started with FREE Demo Class:
*We don’t share your personal info with anyone.
Check out our Privacy Policy for more info.
Training Benefits
Course Module
Cover the fundamentals of key issues in the information security world, including the basics of ethical hacking, information security controls, relevant laws, and standard procedures.
Key topics covered:
Elements of Information Security, Cyber Kill Chain Methodology, MITRE ATT&CK Framework, Hacker Classes, Ethical Hacking, Information Assurance (IA), Risk Management, Incident Management, PCI DSS, HIPPA, SOX, GDPR
Learn how to use the latest techniques and tools to perform foot printing and reconnaissance, a critical pre-attack phase of the ethical hacking process
Hands-On Lab Exercises:
Over 30 hands-on exercises with real-life simulated targets to build skills on how to
- perform foot printing on the target network using search engines, web services, and social networking sites
- Perform website, email, whois, DNS, and network foot printing on the target network
Cover the fundamentals of key issues in the information security world, including the basics of ethical hacking, information security controls, relevant laws, and standard procedures.
Hands-On Lab Exercises:
Over 10 hands-on exercises with real-life simulated targets to build skills on how to
- Perform host, port, service, and OS discovery on the target network.
- Perform scanning on the target network beyond IDS and firewall.
Learn various enumeration techniques, such as Border Gateway Protocol (BGP) and Network File Sharing (NFS) exploits, plus associated countermeasures.
Hands-On Lab Exercises:
Over 20 hands-on exercises with real-life simulated targets to build skills on how to
Perform NetBIOS, SNMP, LDAP, NFS, DNS, SMTP, RPC, SMB, and FTP Enumeration
Learn how to identify security loopholes in a target organization’s network, communication infrastructure, and end systems.
Hands-On Lab Exercises:
Over 5 hands-on exercises with real-life simulated targets to build skills on how to:
- Perform vulnerability research using vulnerability scoring systems and databases
- Perform vulnerability assessment using various vulnerability assessment tools
Learn about the various system hacking methodologies—including steganography, steganalysis attacks, and covering tracks—used to discover system and network vulnerabilities.
Hands-On Lab Exercises:
Over 25 hands-on exercises with real-life simulated targets to build skills on how to:
- Perform Online active online attack to crack the system’s password
- Perform buffer overflow attack to gain access to a remote system
- Escalate privileges using privilege escalation tools
- Escalate privileges in linux machine
- Hide data using steganography
- Clear Windows and Linux machine logs using various utilities
- Hiding artifacts in Windows and Linux machines
Get an introduction to the different types of malware, such as Trojans, viruses, and worms, as well as system auditing for malware attacks, malware analysis, and countermeasures.
Hands-On Lab Exercises:
Over 20 hands-on exercises with real-life simulated targets to build skills on how to:
- Gain control over a victim machine using Trojan
- Infect the target system using a virus
- Perform static and dynamic malware analysis
Key topics covered:
Malware, Components of Malware, APT, Trojan, Types of Trojans, Exploit Kits, Virus, Virus Lifecycle, Types of Viruses, Ransomware, Computer Worms, Fileless Malware, Malware Analysis, Static Malware Analysis, Dynamic Malware Analysis, Virus Detection Methods, Trojan Analysis, Virus Analysis, Fileless Malware Analysis, Anti-Trojan Software, Antivirus Software, Fileless Malware Detection Tools
Learn about packet-sniffing techniques and how to use them to discover network vulnerabilities, as well as countermeasures to defend against sniffing attacks.
Hands-On Lab Exercises:
Over 10 hands-on exercises with real-life simulated targets to build skills
- Perform MAC flooding, ARP poisoning, MITM and DHCP starvation attack
- Spoof a MAC address of Linux machine
- Perform network sniffing using various sniffing tools
- Detect ARP poisoning in a switch-based network
Key topics covered:
Network Sniffing, Wiretapping, MAC Flooding, DHCP Starvation Attack, ARP Spoofing Attack, ARP Poisoning, ARP Poisoning Tools, MAC Spoofing, STP Attack, DNS Poisoning, DNS Poisoning Tools, Sniffing Tools, Sniffer Detection Techniques, Promiscuous Detection Tools
Learn social engineering concepts and techniques, including how to identify theft attempts, audit human-level vulnerabilities, and suggest social engineering countermeasures.
Hands-On Lab Exercises:
Over 4 hands-on exercises with real-life simulated targets to build skills on how to:
Perform social engineering using Various Techniques
Spoof a MAC address of a Linux machine
Detect a phishing attack
Audit an organization’s security for phishing attacks
Key topics covered:
Social Engineering, Types of Social Engineering, Phishing, Phishing Tools, Insider Threats/Insider Attacks, Identity Theft
Learn about different Denial-of-Service (DoS) and Distributed DoS (DDoS) attack techniques, as well as the tools used to audit a target and devise DoS and DDoS countermeasures and protections.
Hands-On Lab Exercises:
Over 5 hands-on exercises with real-life simulated targets to build skills on how to:
Perform a DoS and DDoS attack on a target host
Detect and protect against DoS and DDoS attacks
Key topics covered:
DoS Attack, DDoS Attack, Botnets, DoS/DDoS Attack Techniques, DoS/DDoS Attack Tools, DoS/DDoS Attack Detection Techniques, DoS/DDoS Protection Tools
Understand the various session hijacking techniques used to discover network-level session management, authentication, authorization, and cryptographic weaknesses and associated countermeasures.
Hands-On Lab Exercises:
Over 4 hands-on exercises with real-life simulated targets to build skills on how to:
Perform session hijacking using various tools
Detect session hijacking
Key topics covered:
Session Hijacking, Types of Session Hijacking, Spoofing, Application-Level Session Hijacking, Man-in-the-Browser Attack, Client-side Attacks, Session Replay Attacks, Session Fixation Attack, CRIME Attack, Network Level Session Hijacking, TCP/IP Hijacking, Session Hijacking Tools, Session Hijacking Detection Methods, Session Hijacking Prevention Tools
Get introduced to firewall, intrusion detection system, and honeypot evasion techniques; the tools used to audit a network perimeter for weaknesses; and countermeasures.
Hands-On Lab Exercises:
Over 7 hands-on exercises with real-life simulated targets to build skills on how to:
- Bypass Windows Firewall
- Bypass firewall rules using tunneling
- Bypass antivirus
Learn about web server attacks, including a comprehensive attack methodology used to audit vulnerabilities in web server infrastructures and countermeasures.
Hands-On Lab Exercises:
Over 8 hands-on exercises with real-life simulated targets to build skills on how to:
Perform web server reconnaissance using various tools
Enumerate web server information
Crack FTP credentials using a dictionary attack
Key topics covered:
Web Server Operations, Web Server Attacks, DNS Server Hijacking, Website Defacement, Web Cache Poisoning Attack, Web Server Attack Methodology, Web Server Attack Tools, Web Server Security Tools, Patch Management, Patch Management Tools
Learn about web application attacks, including a comprehensive web application hacking methodology used to audit vulnerabilities in web applications and countermeasures.
Hands-On Lab Exercises:
Over 15 hands-on exercises with real-life simulated targets to build skills on how to:
- Perform web application reconnaissance using various tools
- Perform web spidering
- Perform web application vulnerability scanning
- Perform a brute-force attack
- Perform Cross-Site Request Forgery (CSRF) Attack
- Identify XSS vulnerabilities in web applications
- Detect web application vulnerabilities using various web application security tools
Key topics covered:
Web Application Architecture, Web Application Threats, OWASP Top 10 Application Security Risks – 2021, Web Application Hacking Methodology, Web API, Webhooks, and Web Shell, Web API Hacking Methodology, Web Application Security
Learn about SQL injection attack techniques, injection detection tools, and countermeasures to detect and defend against SQL injection attempts.
Hands-On Lab Exercises:
Over 4 hands-on exercises with real-life simulated targets to build skills on how to
Perform an SQL injection attack against MSSQL to extract databases
Detect SQL injection vulnerabilities using various SQL injection detection tools
Key topics covered:
SQL Injection, Types of SQL injection, Blind SQL Injection, SQL Injection Methodology, SQL Injection Tools, Signature Evasion Techniques, SQL Injection Detection Tools
Learn about wireless encryption, wireless hacking methodologies and tools, and Wi-Fi security tools
Hands-On Lab Exercises:
Over 3 hands-on exercises with real-life simulated targets to build skills on how to:
Foot Print a wireless network
Perform wireless traffic analysis
Crack WEP, WPA, and WPA2 networks
Create a rogue access point to capture data packets
Key topics covered:
Wireless Terminology, Wireless Networks, Wireless Encryption, Wireless Threats, Wireless Hacking Methodology, Wi-Fi Encryption Cracking, WEP/WPA/WPA2 Cracking Tools, Bluetooth Hacking, Bluetooth Threats, Wi-Fi Security Auditing Tools, Bluetooth Security Tools
Learn about mobile platform attack vectors, Android vulnerability exploits, and mobile security guidelines and tools.
Hands-On Lab Exercises
Over 5 hands-on exercises with real-life simulated targets to build skills on how to
Hack an Android device by creating binary payloads
Exploit the Android platform through ADB
Hack an Android device by creating APK file
Secure Android devices using various Android security tools
Key topics covered:
Mobile Platform Attack Vectors, OWASP Top 10 Mobile Risks, App Sandboxing, SMS Phishing Attack (SMiShing), Android Rooting, Hacking Android Devices, Android Security Tools, Jailbreaking iOS, Hacking iOS Devices, iOS Device Security Tools, Mobile Device Management (MDM), OWASP Top 10 Mobile Controls, Mobile Security Tools.
Learn about packet-sniffing techniques and how to use them to discover network vulnerabilities, as well as countermeasures to defend against sniffing attacks.
Hands-On Lab Exercises:
Over 2 hands-on exercises with real-life simulated targets to build skills on how to:
Gather information using Online foot printing tools
Capture and analyze IoT device traffic
Key topics covered:
IoT Architecture, IoT Communication Models, OWASP Top 10 IoT Threats, IoT Vulnerabilities, IoT Hacking Methodology, IoT Hacking Tools, IoT Security Tools, IT/OT Convergence (IIOT), ICS/SCADA, OT Vulnerabilities, OT Attacks, OT Hacking Methodology, OT Hacking Tools, OT Security Tools
Learn different cloud computing concepts, such as container technologies and server less computing, various cloud-based threats and attacks, and cloud security techniques and tools.
Hands-On Lab Exercises:
Over 5 hands-on exercises with real-life simulated targets to build skills on how to:
- Perform S3 Bucket enumeration using various S3 bucket enumeration tools
- Exploit open S3 bucket
- Escalate IAM user privileges by exploiting misconfigured user policy
Key topics covered:
Cloud Computing, Types of Cloud Computing Services, Cloud Deployment Models, Fog and Edge Computing, Cloud Service Providers, Container, Docker, Kubernetes, Serverless Computing, OWASP Top 10 Cloud Security Risks, Container and Kubernetes Vulnerabilities, Cloud Attacks, Cloud Hacking, Cloud Network Security, Cloud Security Controls, Cloud Security Tools
In the final module, learn about cryptography and ciphers, public-key infrastructure, cryptography attacks, and cryptanalysis tools
Hands-On Lab Exercises:
Over 10 hands-on exercises with real-life simulated targets to build skills on how to:
Calculate MD5 hashes
Perform file and text message encryption
Create and use self-signed certificates
Perform email and disk encryption
Perform cryptanalysis using various cryptanalysis tools
Key topics covered:
Cryptography, Encryption Algorithms, MD5 and MD6 Hash Calculators, Cryptography Tools, Public Key Infrastructure (PKI), Email Encryption, Disk Encryption, Cryptanalysis, Cryptography Attacks, Key Stretching
Class Room Training
Fees: INR 15,000/- +18% GST
Course Duration: 3 Months
2 Classes Per Week X 2 Hours Each Day
Batch Timing
Week End Classes | Week Days Classes
Online Self Paced LIVE Training
Fees: INR 15,000/- +18% GST
Course Duration: 3 Months
2 Classes Per Week X 2 Hours Each Day
Batch Timing
Week End Classes | Week Days Classes
Listen from our students!
Trainers Details
- Indian Cyber Security Solutions (ICSS) trainers emphasize blended learning.
- Trainers at ICSS utilize real-life projects and case studies to provide practical knowledge of Ethical Hacking and Hackers.
- ICSS Ethical Hacking trainers in Bangalore have 12+ years of experience in the Networking field.
- Trainers at ICSS are working professionals from the cybersecurity field.
- ICSS trainers provide corporate training to enrich students' knowledge and industry-relevant skills.
- Regular assessments and individual attention are given to students for their progress.
- ICSS Ethical Hacking trainers assist students in resume building and develop their interpersonal skills.
Trainers Details
- Indian Cyber Security Solutions (ICSS) trainers emphasize blended learning.
- Trainers at ICSS utilize real-life projects and case studies to provide practical knowledge of Ethical Hacking and Hackers.
- ICSS Ethical Hacking trainers in Bangalore have 12+ years of experience in the Networking field.
- Trainers at ICSS are working professionals from the cybersecurity field.
- ICSS trainers provide corporate training to enrich students' knowledge and industry-relevant skills.
- Regular assessments and individual attention are given to students for their progress.
- ICSS Ethical Hacking trainers assist students in resume building and develop their interpersonal skills.
Frequently Asked Questions
Can I become a Ethical Hacker in 6 months?
It can take anywhere from a few months to a few years to become an ethical hacker, depending on your level of experience and expertise. For those just starting out, you can enroll for CEH exam preparation course by Indian Cyber Security Solutions which will only take 3 months. ICSS even offers 100% placement assistance.
Who are our instructors and how are they selected?
Professionals who are working with us in developing tools like Face Detection systems, port scanning tools, etc. Besides they are full-time employees of ICSS working in the R&D division. ICSS basically aims to impart the actual programming skills required to get a job in the industry. Moreover learning Ethical Hacking exam preparation courses from industry professionals makes a difference.
What is the best CEH exam preparation course for Ethical Hacking?
The CEH exam preparation course by Indian Cyber Security Solutions stands out as the top choice for ethical hacking, thanks to our skilled trainers and affordable pricing. ICSS has trained over 5000 students, with 500+ successfully placed in the industry.
What is the eligibility for Ethical Hacking?
CEH exam preparation training provided by Indian Cyber Security Solutions is a 3 months course where anyone with a Bachelor's degree (BSc, BTech, BE, BCA, even BA or BCom students) to become an ethical hacker. Candidates having an advanced diploma in network security can also opt for ethical hacking as a career. Even after 12th they can go for Diploma in Cyber Security provided by ICSS.
What is the salary of Ethical Hacker in Hyderabad ?
The average salary for a certified Ethical Hacker is ₹5,21,271 per year in Hyderabad. Indian Cyber Security Solutions have mentored students who got placed at a higher package because of their industry best trainers with 10+ of experience.
Can I learn Ethical Hacking at home?
Yes, it is absolutely possible to learn hacking from home, and it can be highly effective. One of the finest ways to learn hacking in a systematic way is through online instruction. There are many platforms that offer thorough lessons on ethical hacking such as ICSS Ethical Hacking Exam Preparation Training.
What training do you need to be an Ethical Hacker?
One needs to develop technical expertise in areas like programming (especially in languages like Python), establish a thorough grasp of networking and systems, and obtain pertinent certifications like Certified Ethical Hacker (CEH) and CompTIA Security+ to become an ethical hacker.
Do ICSS Provide Placement Assistance?
ICSS is a cyber security company providing services to companies be it private and government agencies across the globe. The requirements come from the companies as we have strong contacts.
What If I Miss A Live Session?
Not a problem even if you miss a live Ethical Hacking session for some reason. If you are attending the LIVE classroom training at our office you can attend any of the parallel classes. Our Admin department is always available to solve any issues faced by students. However, for those attending the online class LIVE, these classes are being recorded and forwarded to all the students.
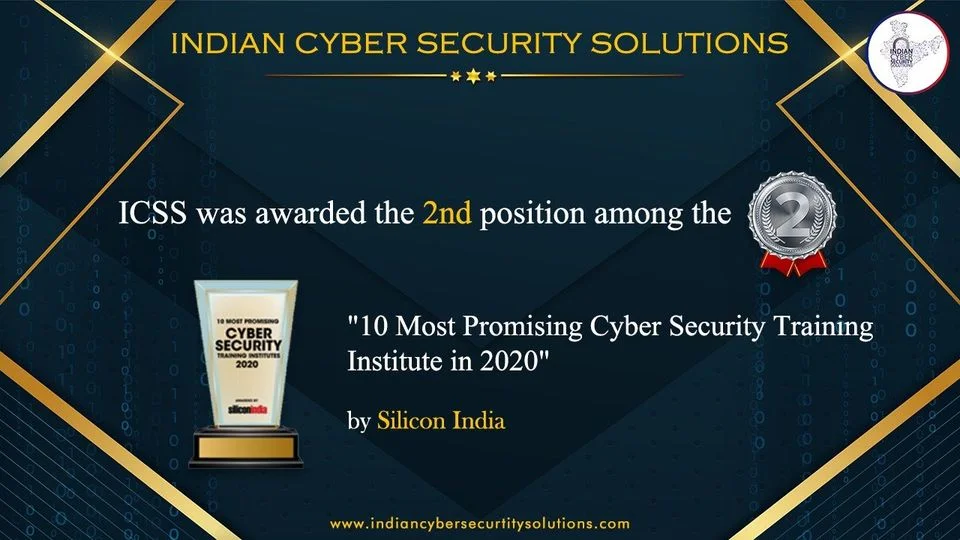
Achievements of our Students
Many of our students have founded Zero-Day Vulnerabilities and also their CVE has published on Exploit-DB. Check their CVE and also read their Blog on Exploit DB.
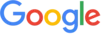
Rabsun Sarkar one of our students has found zero-day vulnerabilities in Google and in the Security Talent Website and also reported for the same.
Rabsun Sarkar one of our students has found zero-day vulnerabilities in Google and in the Security Talent Website and also reported for the same.

CEH Certification Training in Hyderabad
CEH Certification Training in Hyderabad teaches people important skills to protect our city's digital stuff as everything goes digital super fast. Hyderabad, the fourth-most populous city in India is referred as "The City of Pearls" because of its history of pearl trafficking. The metropolitan area of Hyderabad, which is 7,257 km2 in size, offers a varied terrain with lovely rivers and scenic splendor. It ranks as India's fifth-largest metropolitan economy with a remarkable output of US$74 billion. Hyderabad has a dry climate, and the wintertime lows of 10 degrees Celsius make for a wonderful addition to the educational process.
The CEH Certification Training in Hyderabad is the perfect opportunity for aspiring professionals to enhance their cybersecurity skills. Indian Cyber Security Solutions has trained more than 1298+ students and takes pride in being the premier CEH exam preparation training center in Hyderabad. With around 20+ penetration testers and ethical hackers working with Indian Cyber Security Solutions, it is quite easy to provide world-class practical exam preparation training which is required for CEH certification.
Learn ethical hacking techniques while immersing yourself in the city's vibrant IT scene. While exploring this magnificent city, make sure to consider visiting the following places during your weekend getaway:












































 (9).png)
 (18).png)
 (23).png)
 (16).png)