Indian Cyber Security Solutions
in association with
Indian Institute of Cyber Security
CEH Training in India - C|EHv12
(Certified Ethical Hacker) Course
Course Fees: INR 15,000/-
CEH Training in India, particularly C|EH v12, is a widely respected certification within the cybersecurity field. Indian Cyber Security Solutions provides a comprehensive CEH Exam Preparation Training that lasts for three months, available both online and in a classroom setting, based on the latest version, v12. Our core team consists of highly skilled specialists with practical experience in cybersecurity, going beyond theoretical knowledge. Over 130 instructors, all experts in ethical hacking, are part of our extensive network.
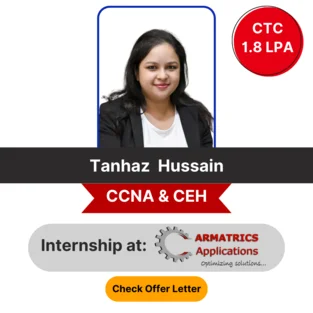
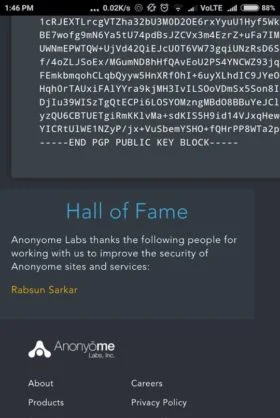
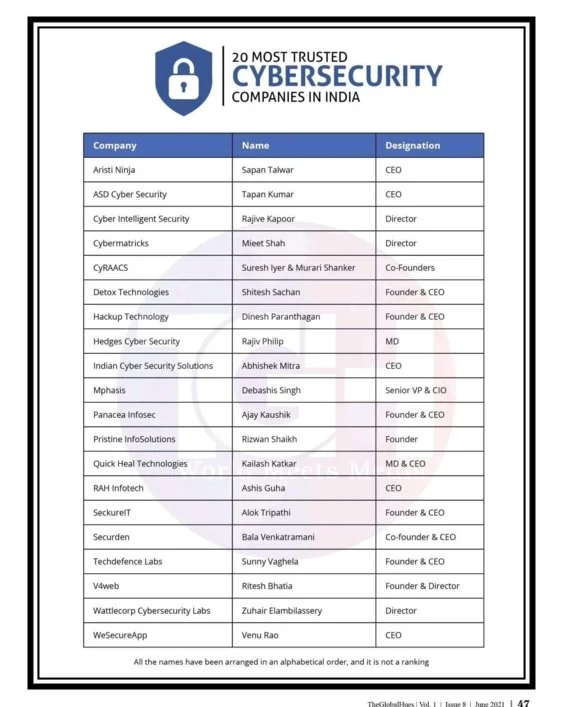
The CEH Training in India opens doors to the cybersecurity industry and is recognized in over 160 countries. Many multinational corporations now require CEH certification for security-related positions. Respected global organizations such as Infosys, Cognizant, Wipro, ATOS, and Intel benefit from the expertise of our trainers. Being named one of Silicon India's "10 Most Promising Cyber Security Consultants for 2023" is an honor. We offer strong placement support for students pursuing corporate careers. Indian Cyber Security Solutions takes pride in being the top-choice destination for CEH exam preparation training in India, attracting more than 1890 students from around the world each year. Our goal is to provide people with the information and abilities they need to properly defend against online threats. We think we're making the digital world safer for both organizations and individuals with our CEH exam training and placement support.
Enroll for
Online Live Class
Get Started with FREE Demo Class
Note: "Certified Ethical Hacker" and "CEH" is a registered trademarks of EC-Council and this course is not licensed, endorsed, or affiliated with EC-Council in any way.
UNIVERSITY TRAINING PARTNER'S
Key Highlights
No Cost EMI & Educational Loan
100% Placement Support
3 Months Training
Classroom Training
Online Training
Program Duration
3 Months
Get First 2 Classes FREE
Enroll Now !!
Please contact us using the form below
No Advance Payment Required
Learning Format
Classroom & Online
Why Join CEH Training at ICSS

Reviews
4.8
1,09,233
Students Enrolled in
Indian Cyber Security Solutions

Reviews
4.8
CEH Course in India
Get Ahead in the Tech Industry
CEH Course in India at ICSS provides valuable ethical hacking skills that can boost your cybersecurity career. What sets Indian Cyber Security Solutions apart is its team of experienced and certified trainers who bring real-world knowledge to the classroom.
We offer hands-on exam preparation training and practical exercises that simulate real-world cyber attacks, giving you the skills necessary to identify vulnerabilities and effectively secure systems. In addition, the course is designed to be accessible, with classroom and online options that will make it easier for students and employees working across India.
CEH exam preparation course is designed to suit both beginners and experienced professionals seeking to advance their careers in the cyber security field. Upon completion, you will earn an internationally recognized CEH certification, which opens the door to exciting career opportunities in cybersecurity.
Indian Cyber Security Solutions is committed to providing assistance you let you achieve your cyber security goals and prepare for a successful career in these top in -demand jobs. We offer CEH course in India that provide not only information and technical skills but also industry experts. Take the first step towards a rewarding cybersecurity career with ICSS.
Best CEH Training Institute in India
Secure Your Future with Us
Best CEH Training Institute in India is Indian Cyber Security Solutions. The complete CEH exam preparation training provided by ICSS gives students the know-how and abilities they need to succeed in the ethical hacking industry. The need for cybersecurity specialists is growing and ICSS's exam training will provide you the skills necessary to fill this need.
Additionally, we provide flexible learning alternatives, such as in-person and online courses, making it available to students and working adults throughout India. We stand out as the best CEH training institute in India because of our dedication to offering high-quality instruction at reasonable costs.
Our courses are suitable for everyone, from beginners to working professionals. The CEH course highlights the value of ethical and responsible hacking techniques in addition to penetration testing and vulnerability assessment. You will gain hands-on, practical instruction because of our knowledgeable professors' real-world experience that they bring to the classroom.
The dedication of ICSS to producing ethical hackers who exercise their abilities properly sets us distinct. We are the top CEH exam training Institute if you're trying to start or enhance your career in cybersecurity. The best option for assisting you in reaching your goals is us because of our excellent exam training, knowledgeable instructors, ethical attitude and widespread notoriety.
Course Eligibility
Eligibility Criteria
Technical Background
Individuals with a Technical foundation can expand their expertise by enrolling in Ethical Hacking course.
Enroll Now !!
Please contact us using the form below
Non-Technical Background
Students from non-technical disciplines can also pursue Ethical Hacking course.
Enroll Now !!
Please contact us using the form below