Diploma in Cyber Security Training in India with Placement by Indian Cyber Security Solutions
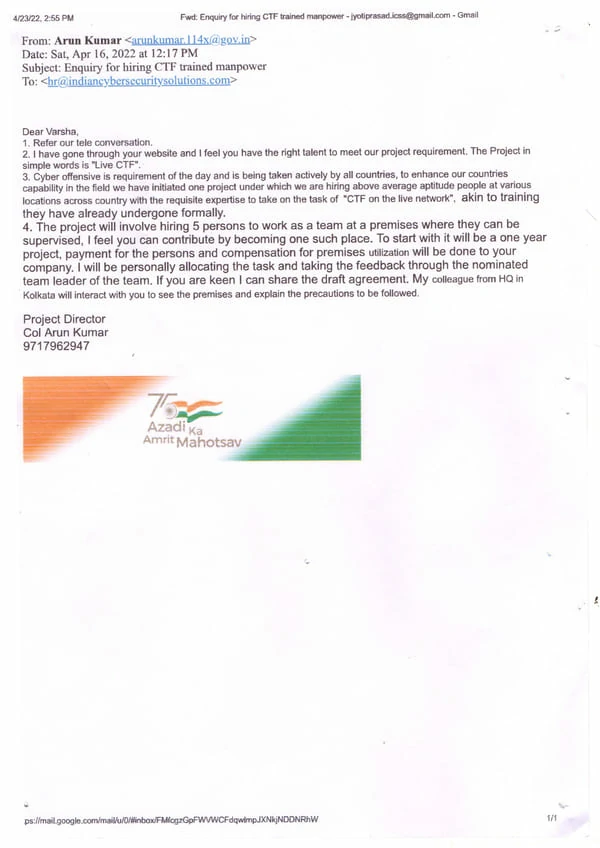
Diploma in Cyber Security Training in India at Indian Cyber Security Solutions (ICSS) provides you with industry-ready expertise to tackle the dynamic challenges of the cybersecurity world. ICSS is renowned for safeguarding India's cyber safety, successfully defending against state-sponsored attacks, and securing critical platforms like the Co-Win vaccination portal. Imagine state-sponsored attackers from Pakistan hacking Indian airport websites and the NSG National Security Guard website. ICSS not only thwarted these attacks but turned the tables, countering and attacking the Islamabad Airport website and servers containing many other websites. Our comprehensive course includes safe coding practices, encryption, ethical hacking, network security, WAPT, NPT etc. You'll have the opportunity to apply your knowledge in real-world situations, participate in real life projects, and complete practical projects, ensuring a thorough understanding of both theoretical and practical aspects of cybersecurity.
Diploma in Cyber Security Training in India at ICSS is taught by over 130 experienced professors, including skilled ethical hackers who have worked with prestigious MNCs like Infosys, Cognizant, Wipro, ATOS, and Intel. Our institute boasts fully equipped computer labs featuring the latest hardware and software essential for effective cybersecurity training. Recognized as one of the "10 Most Promising Cyber Security Consultants for 2023" by Silicon India, ICSS is committed to providing excellence in cybersecurity education. We also offer substantial job placement assistance, helping you start your career with top-tier companies. Join ICSS to be part of a community dedicated to building a safer digital future. Enroll in our Diploma in Cyber Security Training today and begin your journey towards a successful career in cybersecurity.
Diploma in Cyber Security Training in India, designed by experienced penetration testers with over 15 years of experience, is your gateway to a rewarding job in cybersecurity. This comprehensive diploma signifies deep understanding and commitment, making you stand out to employers. Indian Cyber Security Solutions offers a robust framework, equipping you for roles like penetration tester or cybersecurity expert.











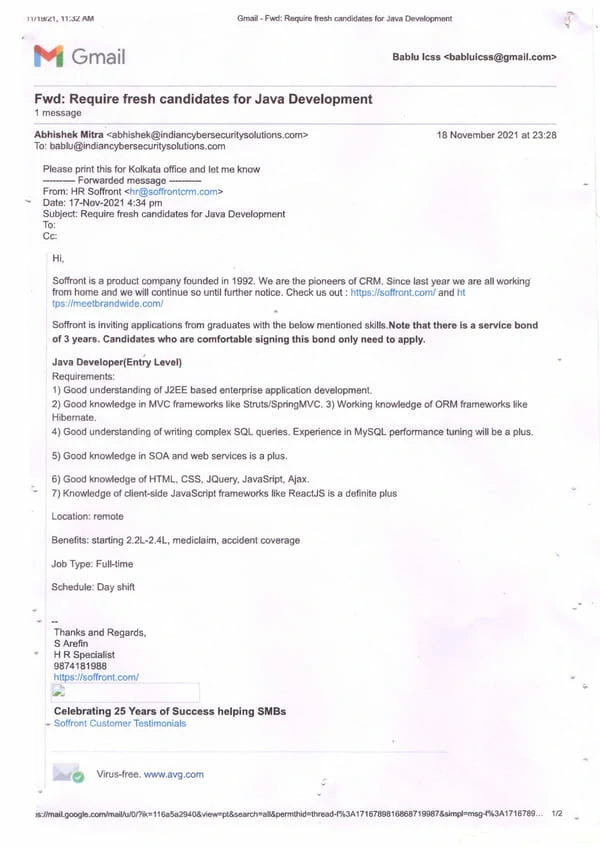
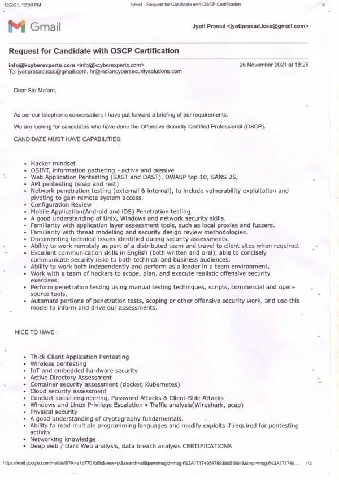
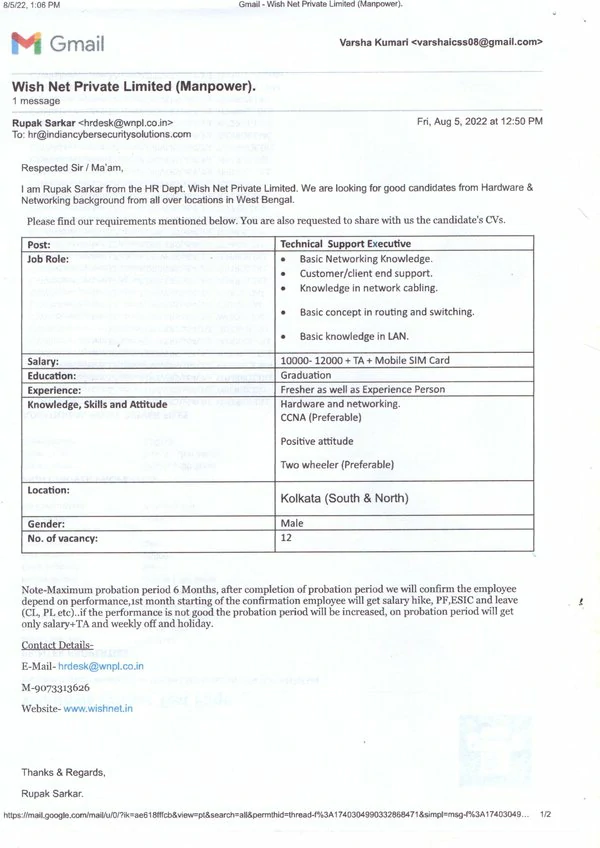
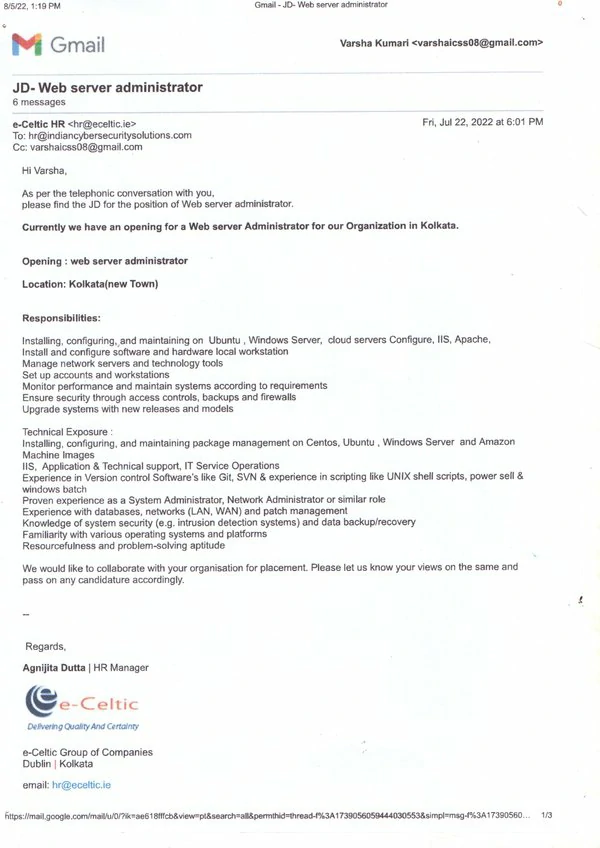
With attractive packages and promising career growth, our graduates are making significant strides in the industry. The images of our placed students, along with their impressive packages, highlight the real-world impact of our comprehensive training program.
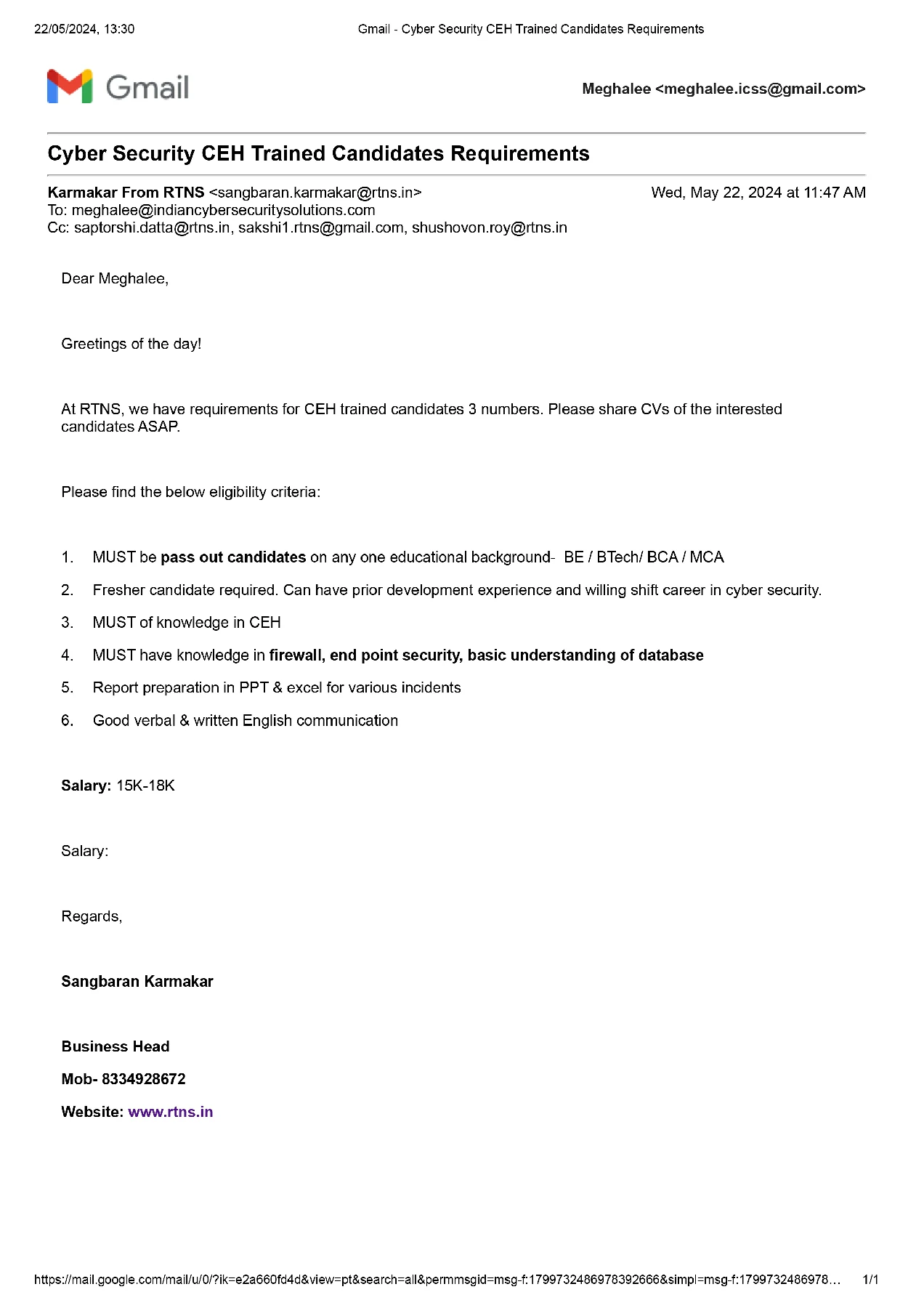
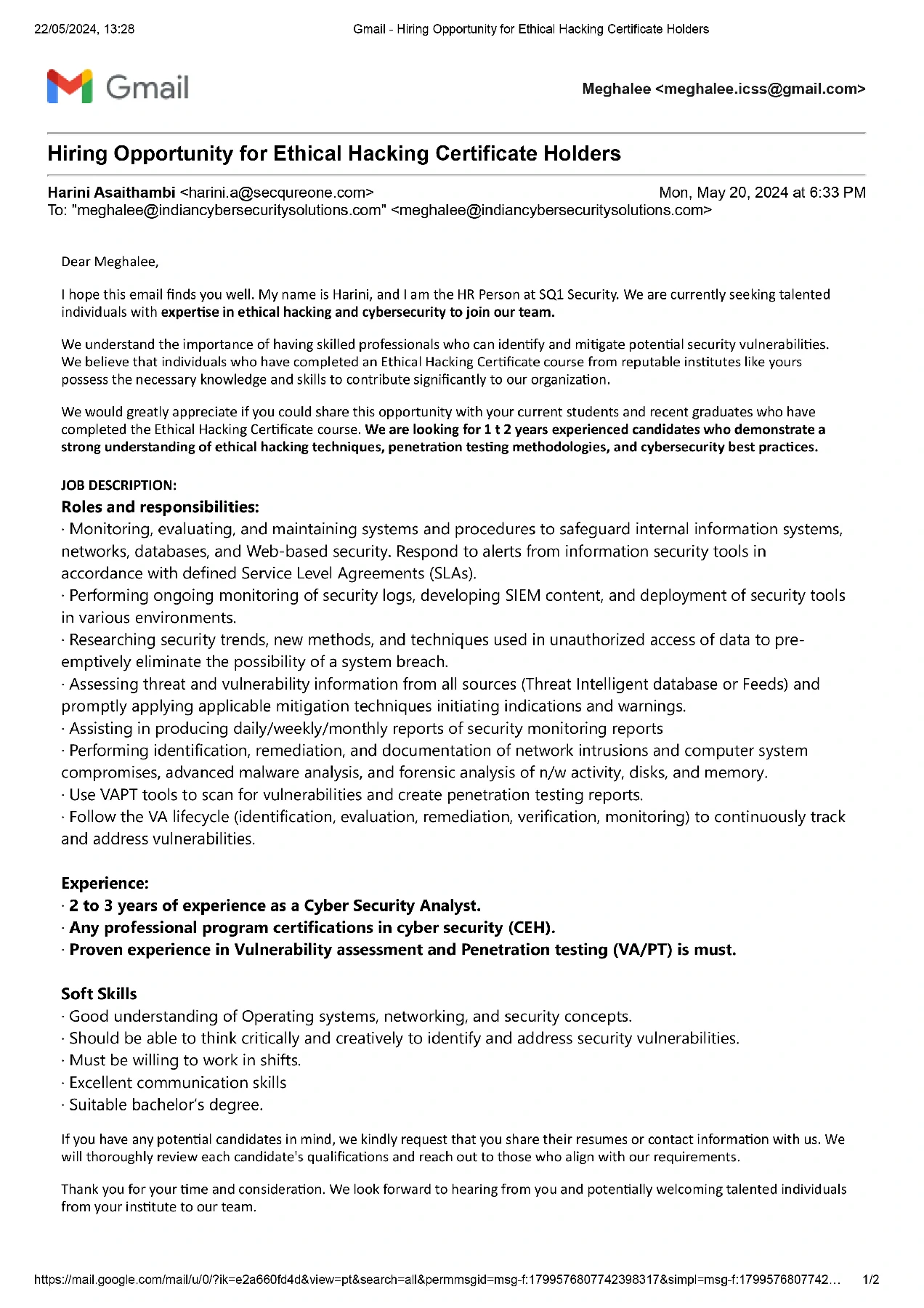
Our recent placement records speak volumes about the success of our Diploma in Cyber Security Training in India. At Indian Cyber Security Solutions (ICSS), we pride ourselves on providing top-notch education that prepares students for the demanding cybersecurity job market. Our students have secured prestigious positions in leading MNCs such as Wipro, TCS, Amazon, and many more.
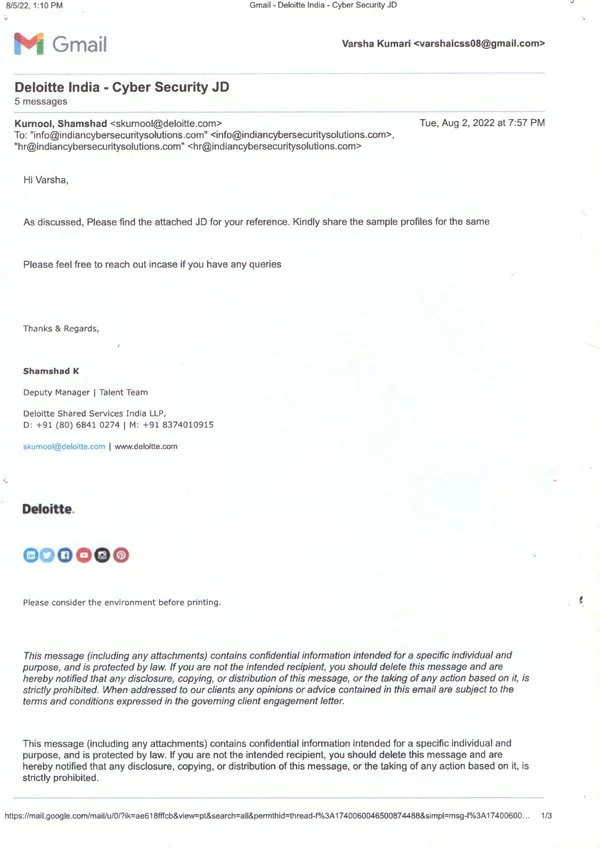
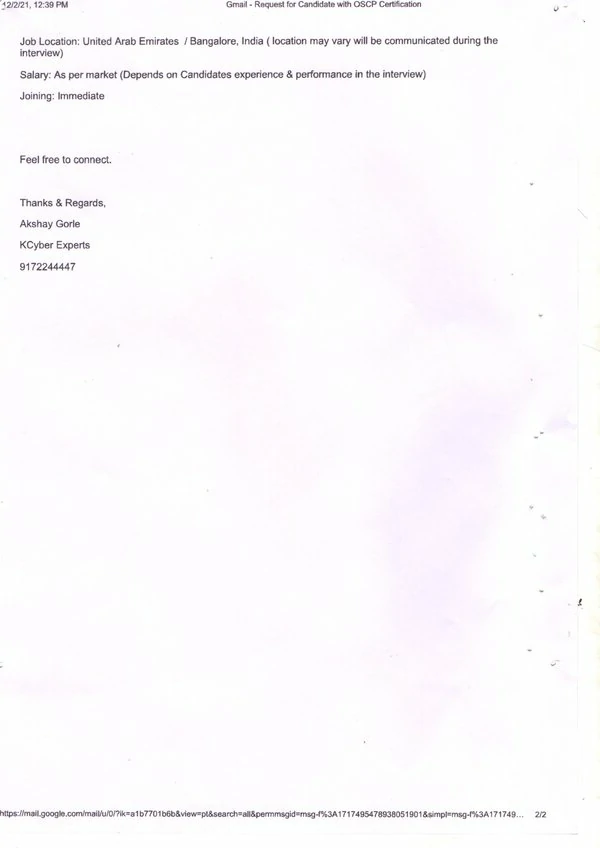
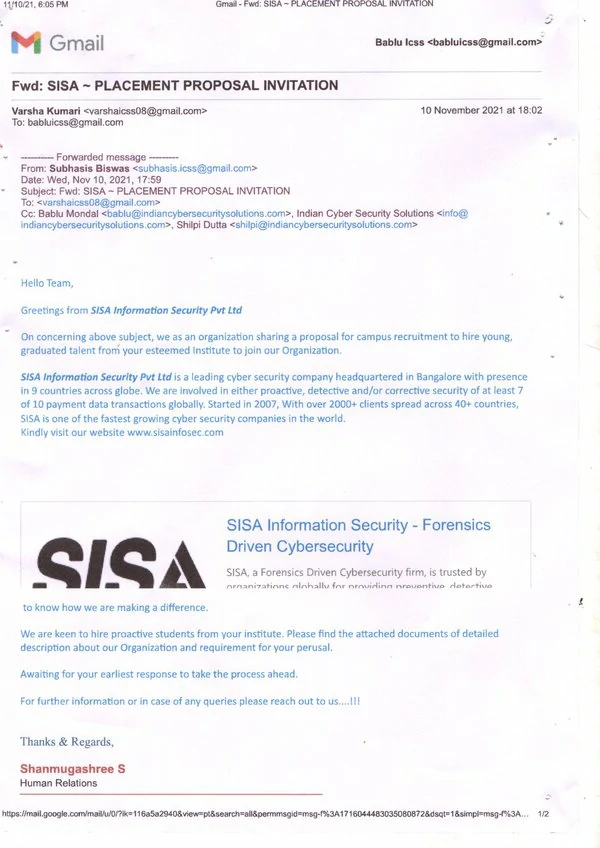
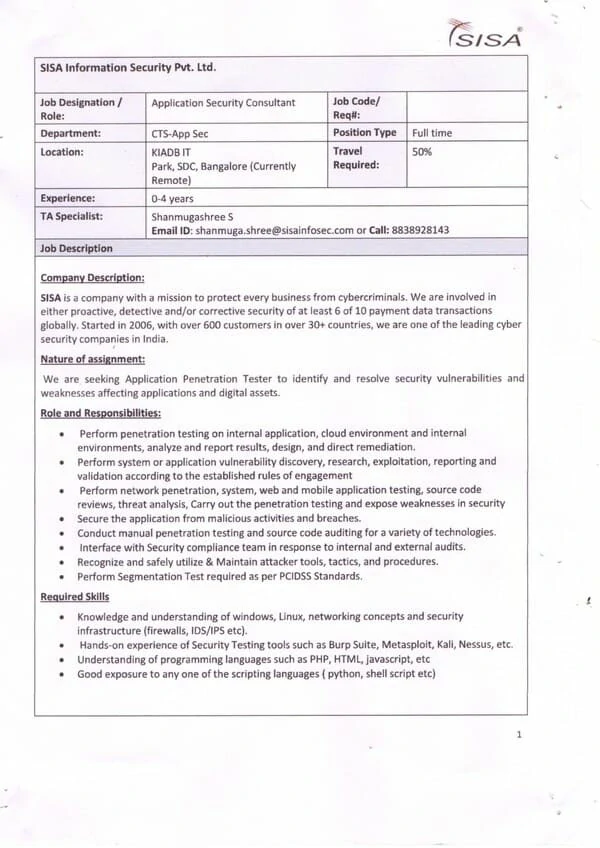
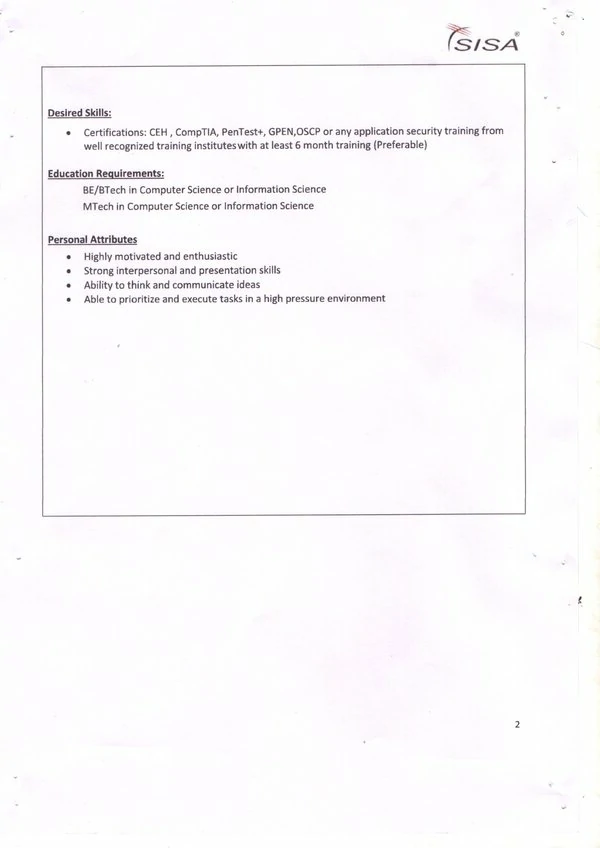
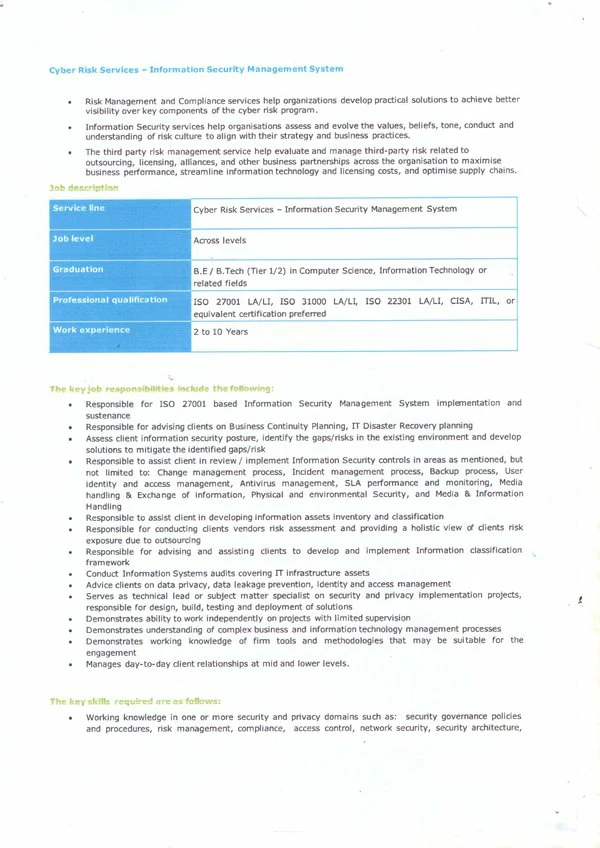
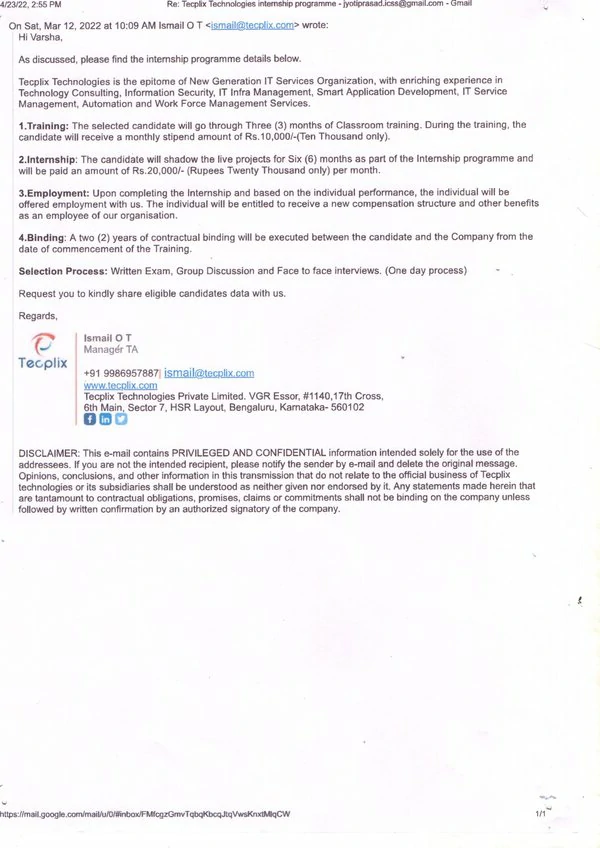
Join our Diploma in Cyber Security Training in India and take advantage of our strong industry connections and proven placement track record. Secure your future with ICSS and become a part of the elite group of cybersecurity professionals who are shaping the future of digital security.
Diploma in Cyber Security Course in India
Diploma in Cyber Security Course in India provided by Indian Cyber Security Solutions (ICSS) opens doors to a promising career in the cybersecurity field. Our Diploma in Cyber Security Training in India begins with fundamental cybersecurity techniques and progresses to more advanced technologies like reverse engineering and penetration testing. This structured approach ensures that you build a solid foundation before tackling more complex concepts, making the learning process smooth and comprehensive. With hands-on projects and real-world scenarios, you will develop the skills necessary to defend against cyber threats and vulnerabilities.
Diploma in Cyber Security Course in India at ICSS is taught by highly qualified professors who bring real-world experience to the classroom. This is particularly beneficial for working professionals looking to upgrade their skills without disrupting their jobs. Our Diploma in Cyber Security Training in India is designed to benefit both students and professionals already in the workforce, providing flexible learning alternatives so you can choose the option that best fits your schedule. The success stories of our students highlight the effectiveness of our program, with many forging impressive careers and making significant impacts in the cybersecurity sector. Enroll in our Diploma in Cyber Security Course today and embark on a journey that will shape the future of cybersecurity in India. Your cybersecurity career starts here! Don't wait; protect the digital world with us.
Diploma in Cyber Security Course in India offered by Indian Cyber Security Solutions is a comprehensive program designed to equip individuals with the necessary knowledge and skills to excel in the field of cybersecurity. With a focus on practical training and an industry-relevant curriculum, this course is ideal for both beginners and experienced professionals seeking to enhance their cybersecurity expertise. This course covers a wide range of topics, starting from the fundamentals of cybersecurity to advanced concepts such as network security, web application security, ethical hacking, and digital forensics. The curriculum is carefully designed to provide a step-by-step learning approach, ensuring that students understand each concept thoroughly before moving on to the next. One of the key advantages of the Diploma in Cyber Security Training in India is the expertise of the faculty. The instructors at Indian Cyber Security Solutions are experienced professionals with in-depth knowledge and practical experience. They bring their industry experience into the classroom. So if you are looking for a Diploma in Cyber Security Course in India, ICSS is your first preference.
The course also emphasizes hands-on training and practical exercises, allowing students to apply their knowledge in real-world scenarios. The institute provides well-equipped computer labs with the latest tools and software necessary for cybersecurity training. This enables students to gain practical experience in using industry-standard cybersecurity tools and techniques. By enrolling in the Diploma in Cyber Security Training in India, students not only gain theoretical knowledge but also have the opportunity to work on real-world projects and case studies. This practical exposure helps them develop problem-solving skills and enhances their understanding of the concepts learned in the classroom. It also prepares them to tackle real-world cybersecurity challenges effectively. One of the key advantages of the Diploma in Cyber Security Course in India is the expertise of the faculty. The instructors at Indian Cyber Security Solutions are experienced professionals with in-depth knowledge and practical experience in the field of cybersecurity. They bring their industry experience into the classroom, providing real-world insights and practical examples to enhance the learning experience.
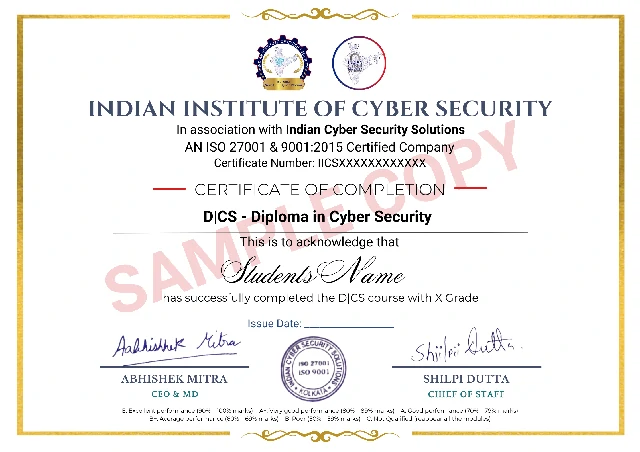
Indian Cyber Security Solutions offers a Diploma in Cyber Security Certification in India, providing an exceptional opportunity for those seeking a career in cybersecurity. This program prepares you for the growing demand in the field, offering industry-recognized certification upon completion. With assistance in job placement and partnerships with top cybersecurity firms, the certification opens doors to a wide range of global employment opportunities. Gain practical experience and industry recognition, making it a wise investment in your professional future in the digital world.
Indian Cyber Security Solutions & Indian Institute of Cyber Security
Diploma in Cyber Security Training Institute in India
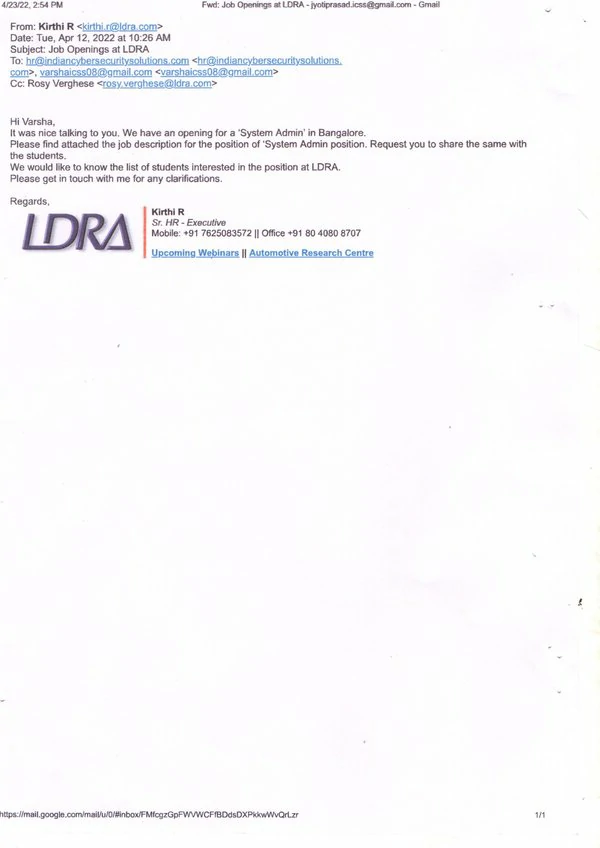
2024 Ongoing Campus Placement
Diploma in Cyber Security Training Institute in India: Indian Cyber Security Solutions (ICSS) offers world-class education and practical training for a secure digital future. We've earned a strong reputation for delivering top-tier training and support, catering to both beginners and those seeking advanced expertise. Our Diploma in Cyber Security Training in India module, spanning 12 months, is meticulously crafted to equip you with the most practical insights. This comprehensive training ensures that you are well-prepared to tackle real-world cybersecurity challenges with confidence and competence.
Diploma in Cyber Security Training Institute in India at ICSS goes the extra mile by inviting guest instructors from the industry to our training facility. They bring invaluable real-world experiences directly to you, ensuring you're well-prepared for the challenges of the cybersecurity field. Indian Cyber Security Solutions has an outstanding track record of successful placements, ensuring that our students are ready for the workforce. At ICSS, we're not merely a training institute; we're your partner on the journey towards a secure digital future. Our commitment goes beyond education; it extends to being your companion as you embark on a career in cybersecurity. Join us today and together, we'll pave the way to a safer digital world. Protect, defend, and secure with Indian Cyber Security Solutions through our Diploma in Cyber Security Training in India.
Since 2016, Indian Cyber Security Solutions (ICSS) has become the leading Diploma in Cyber Security Training Institute in India. Our program is designed to equip students with the skills needed to excel in the cybersecurity field. With a strong emphasis on practical, hands-on training, our graduates are well-prepared for the challenges of the industry.
ICSS boasts a stellar placement record, with students securing positions in prestigious companies like Wipro, TCS, and Amazon. Located in Sector V, Kolkata's IT hub, we provide students with excellent opportunities for networking and on-campus recruitment.
Our success over the years is a testament to our commitment to quality education and student success. Join ICSS and become part of a legacy of excellence in cybersecurity training. Enroll in our Diploma in Cyber Security Training Institute in India today and take the first step towards a promising career. Visit our website to learn more and register now!