Diploma in Advanced Cloud & Network Security
with Placement by Indian Cyber Security Solutions
Cybersecurity training in India with placement opportunities is what every tech enthusiast is looking for. Indian Cyber Security Solutions in association with the Indian Institute of Cyber Security brings in the most practical hands-on cybersecurity training in India. Get the most valuable certificate recognized by MNC’s from the Indian Institute of Cyber Security.
The Certified Cyber Security Professional (C|CSP) course is meticulously designed to cater to students from technical backgrounds such as BCA, MCA, BTech, and BSc in Computer Science. The course is structured into two comprehensive levels, ensuring a robust learning curve that caters to both beginners and advanced learners.
Diploma in Advanced Cloud & Network Security in India, designed by experienced penetration testers with over 15 years of experience, is your gateway to a rewarding job in cybersecurity. This comprehensive training signifies deep understanding and commitment, making you stand out to employers. Indian Cyber Security Solutions offers a robust framework, equipping you for roles like penetration tester or cybersecurity expert.







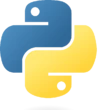




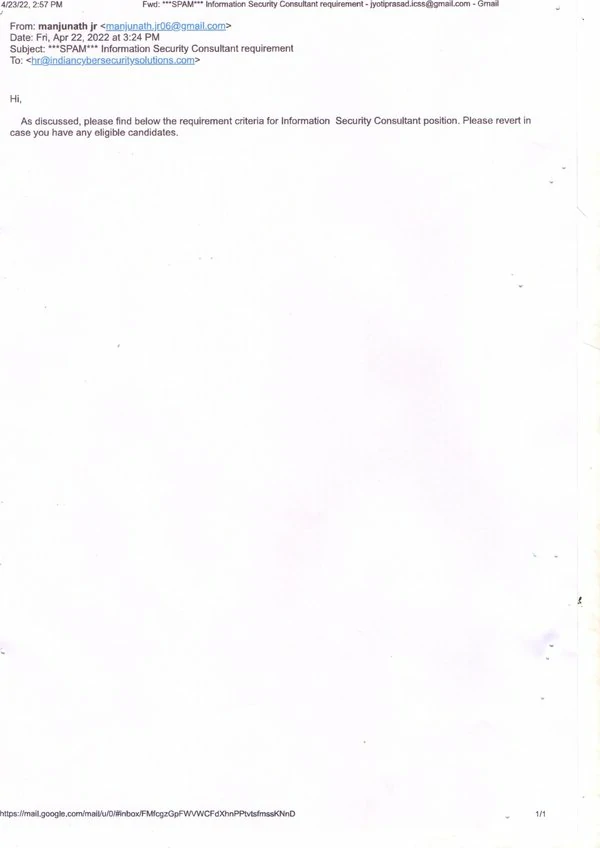
With attractive packages and promising career growth, our graduates are making significant strides in the industry. The images of our placed students, along with their impressive packages, highlight the real-world impact of our comprehensive training program.
Our recent placement records speak volumes about the success of our Diploma in Advanced Cloud & Network Security in India. At Indian Cyber Security Solutions (ICSS), we pride ourselves on providing top-notch education that prepares students for the demanding cybersecurity job market. Our students have secured prestigious positions in leading MNCs such as Wipro, TCS, Amazon, and many more.
Join our Diploma in Advanced Cloud & Network Security in India and take advantage of our strong industry connections and proven placement track record. Secure your future with ICSS and become a part of the elite group of cybersecurity professionals who are shaping the future of digital security.
Diploma in Advanced Cloud & Network Security Training Course in India by Indian Cyber Security Solutions is the highest-rated award-winning cybersecurity certification course
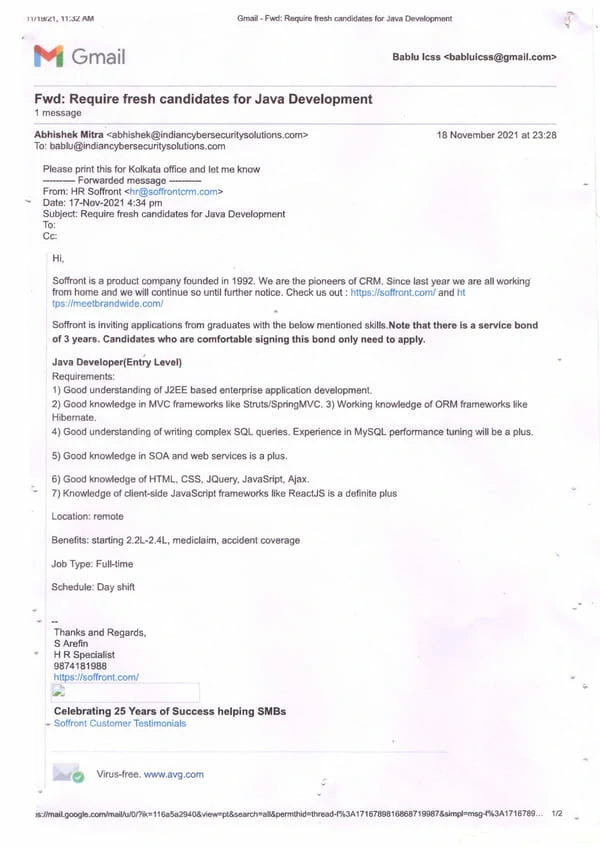
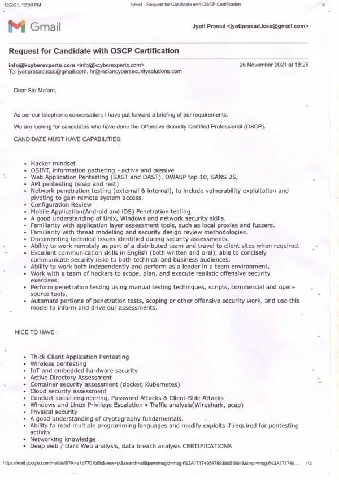
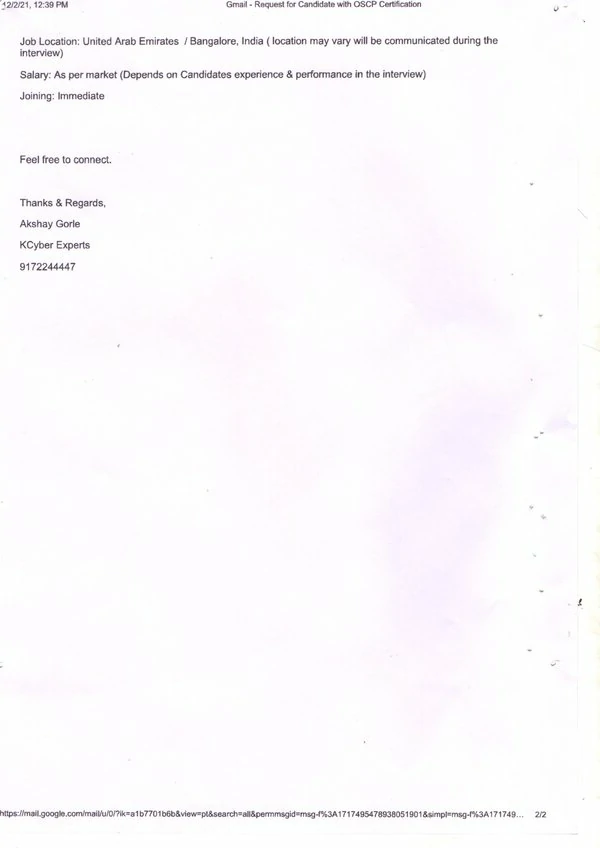
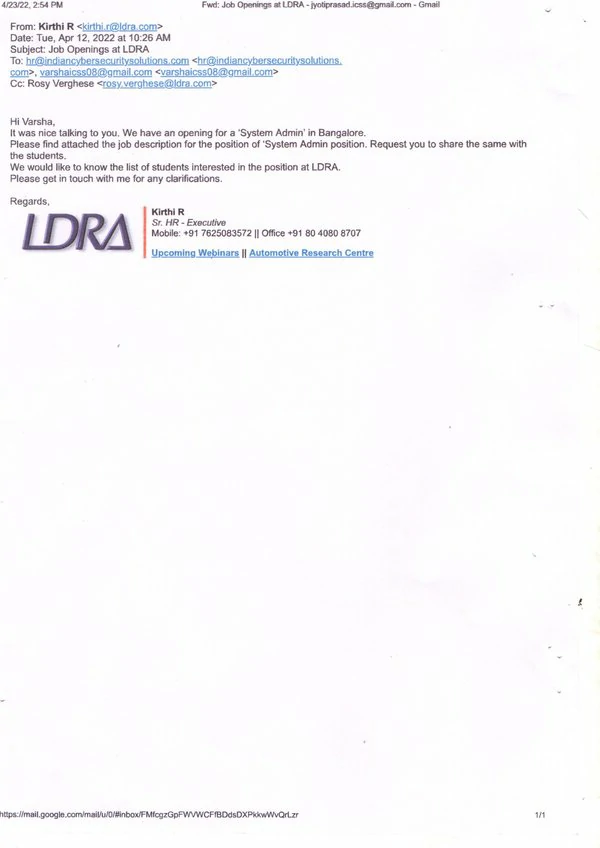
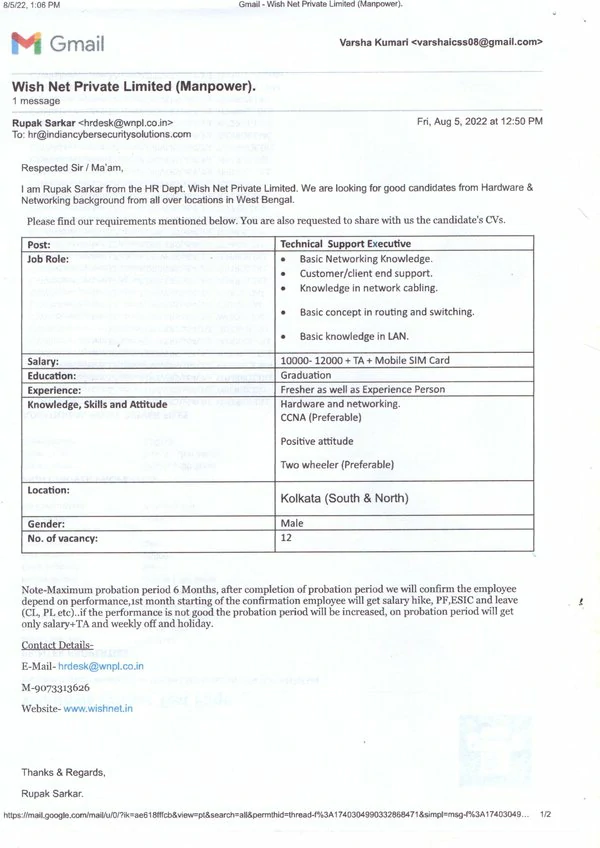
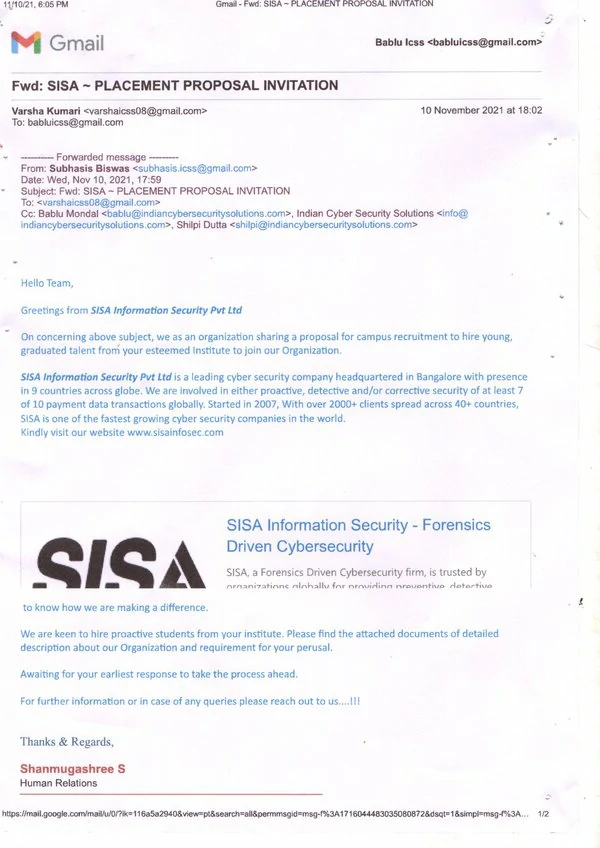
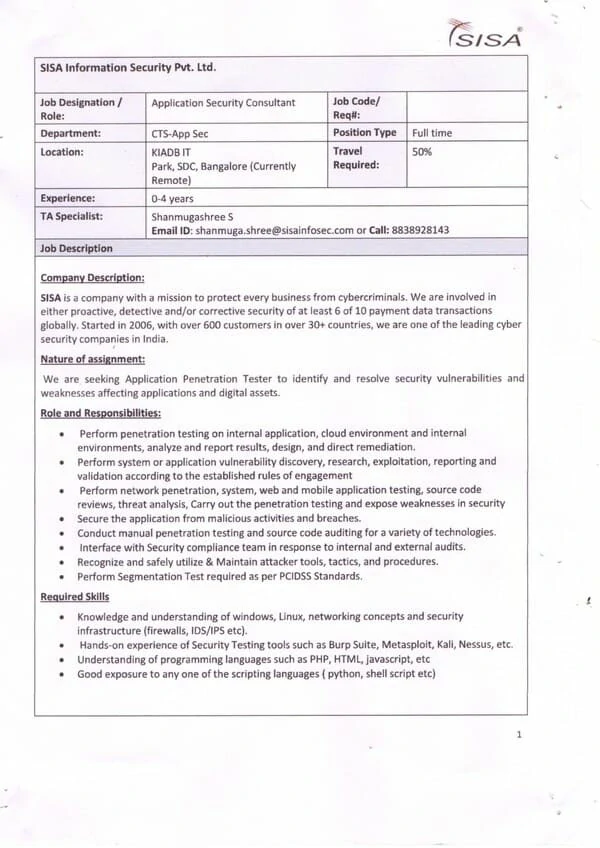
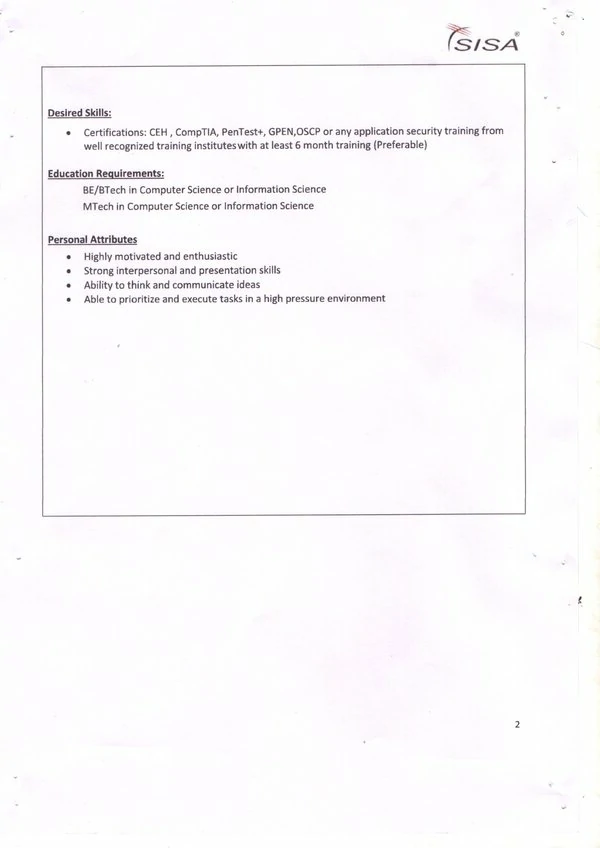
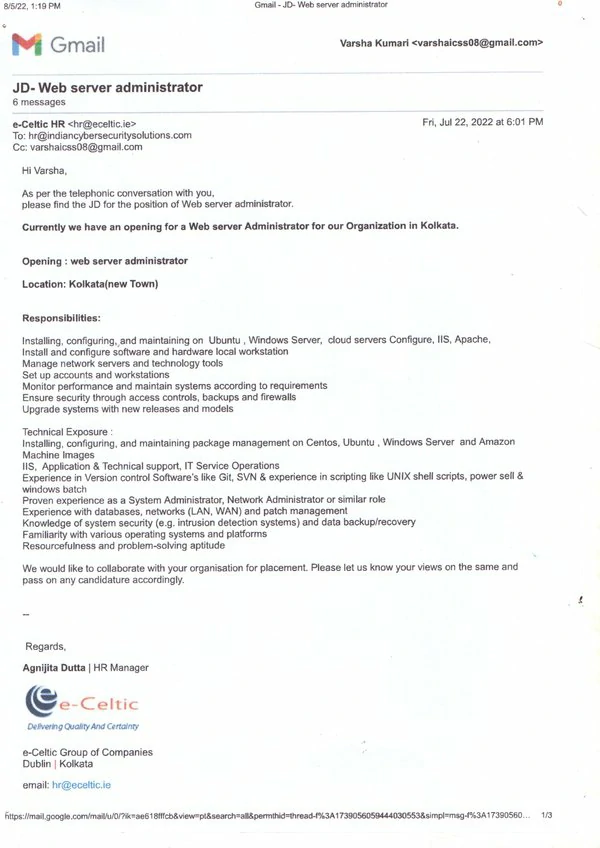
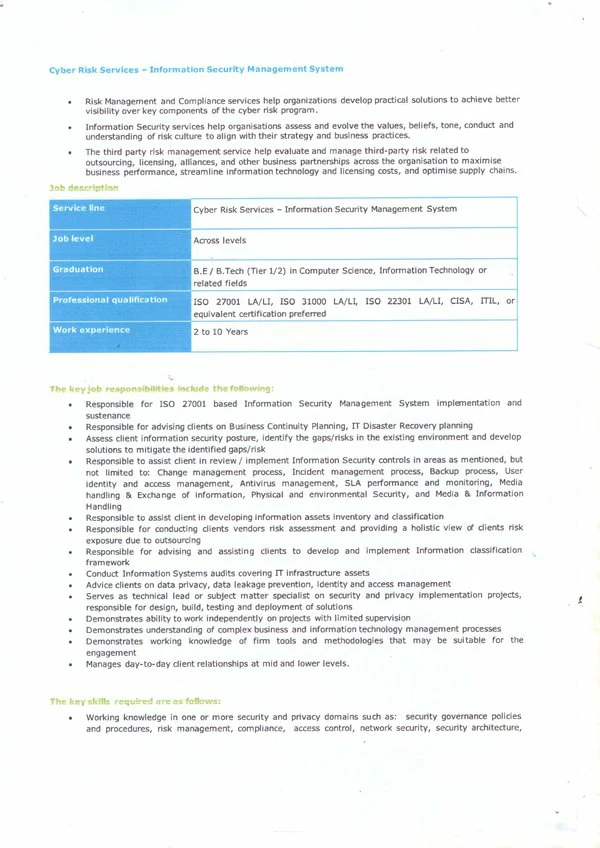
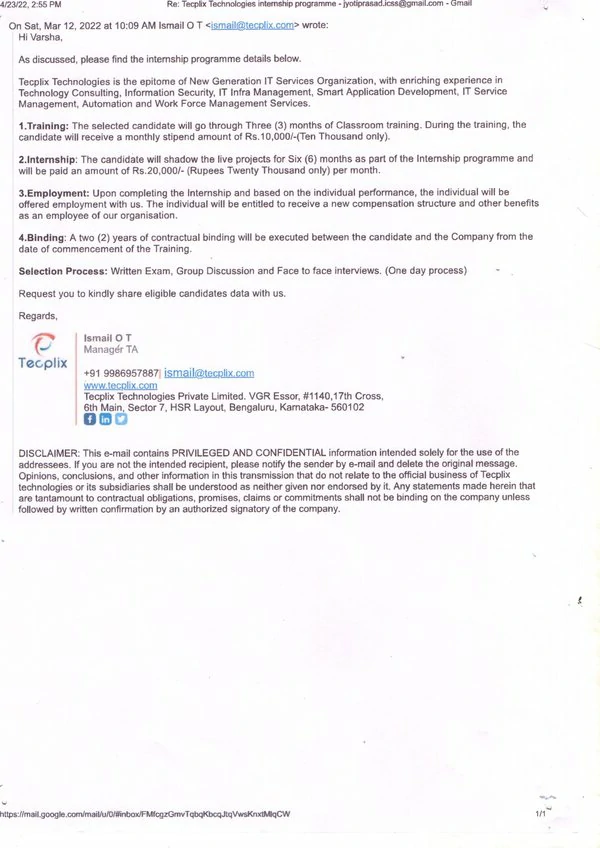
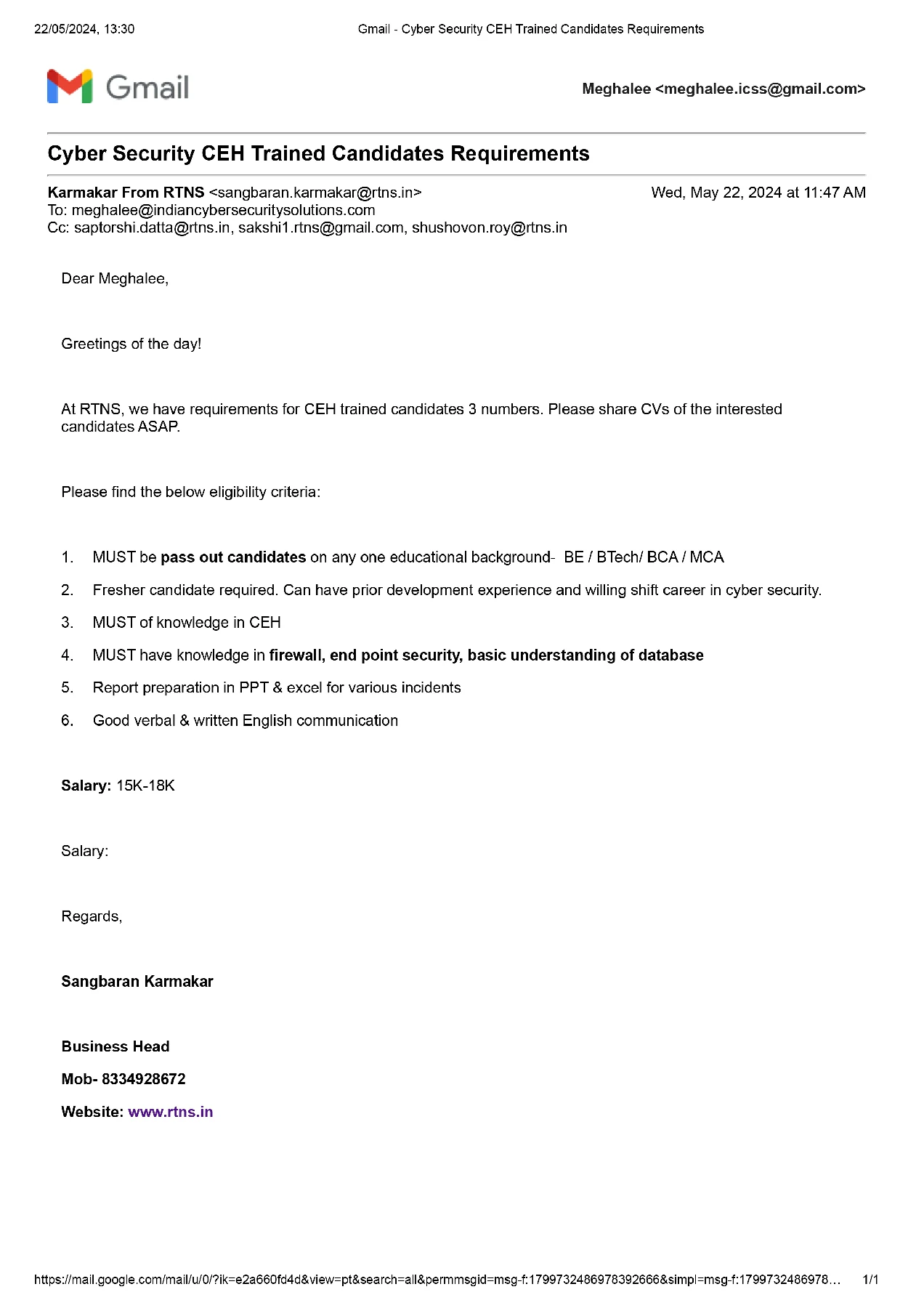
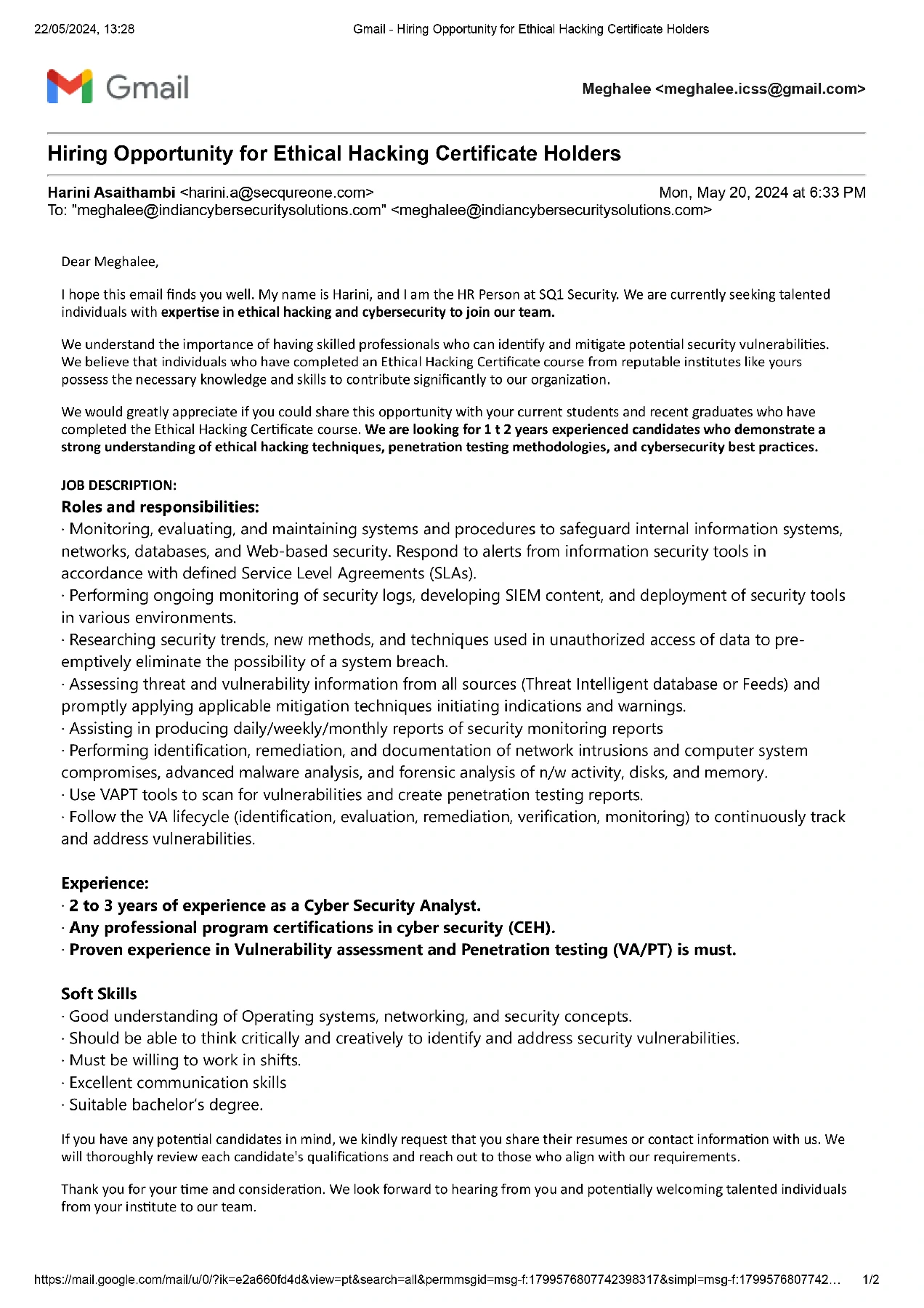
Cybersecurity course in India opens up a vast opportunity for placements. Check out our placement records and emails which we receive regularly from companies across India. With a proven track record, our graduates are highly sought after by companies across the country. Regular emails from employers seeking skilled professionals underscore our successful placement record. The cybersecurity training in India is designed to meet industry standards, ensures that students are job-ready upon graduation. The combination of comprehensive training, practical experience, and strong industry connections makes cybersecurity course in India (C|CSP) the top choice for aspiring cybersecurity professionals.
In fact, as per the 2018 Cost of Data Breach Study sponsored by IBM, the global average cost of data breach comes around $3.62 million. As these hacking skills can be used in a bad way, our Diploma in Diploma in Advanced Cloud & Network Security in Kolkata will help you how you can use the same skills to protect the intellectual property of organizations and individuals and become a white hat hacker. During the course of ethical hacking, you will develop the ability to measure and mitigate threats and find out where your organization is more vulnerable to be hacked. Most of our students found Zero-day vulnerabilities. If you are looking to build a career in the field of cybersecurity you can enroll in our Diploma in Cyber Security Course in Kolkata.
Diploma in Advanced Cloud & Network Security Course in India offered by Indian Cyber Security Solutions is a comprehensive program designed to equip individuals with the necessary knowledge and skills to excel in the field of cybersecurity. With a focus on practical training and industry-relevant curriculum, this course is ideal for both beginners and experienced professionals seeking to enhance their cybersecurity expertise. This course covers a wide range of topics, starting from the fundamentals of cybersecurity to advanced concepts such as network security, web application security, ethical hacking, and digital forensics. The curriculum is carefully designed to provide a step-by-step learning approach, ensuring that students understand each concept thoroughly before moving on to the next. One of the key advantages of the Cyber Security Taining Course in India is the expertise of the faculty. The instructors at Indian Cyber Security Solutions are experienced professionals with in-depth knowledge and practical experience in the field of cybersecurity. They bring their industry experience into the classroom, providing real-world insights and practical examples to enhance the learning experience. So if you are looking for Diploma in Advanced Cloud & Network Security Course in India, ICSS’s is your first preference.
The course also emphasizes hands-on training and practical exercises, allowing students to apply their knowledge in real-world scenarios. The institute provides well-equipped computer labs with the latest tools and software necessary for cybersecurity training. This enables students to gain practical experience in using industry-standard cybersecurity tools and techniques. By enrolling in the Diploma in Advanced Cloud & Network Security in India, students not only gain theoretical knowledge but also have the opportunity to work on real-world projects and case studies. This practical exposure helps them develop problem-solving skills and enhances their understanding of the concepts learned in the classroom. It also prepares them to tackle real-world cybersecurity challenges effectively. One of the key advantages of the Cyber Security Course in India is the expertise of the faculty. The instructors at Indian Cyber Security Solutions are experienced professionals with in-depth knowledge and practical experience in the field of cybersecurity. They bring their industry experience into the classroom, providing real-world insights and practical examples to enhance the learning experience.
Indian Cyber Security Solutions offers a Cyber Security Training Certification in India, providing an exceptional opportunity for those seeking a career in cybersecurity. This program prepares you for the growing demand in the field, offering industry-recognized certification upon completion. With assistance in job placement and partnerships with top cybersecurity firms, the certification opens doors to a wide range of global employment opportunities. Gain practical experience and industry recognition, making it a wise investment in your professional future in the digital world.
Indian Cyber Security Solutions & Indian Institute of Cyber Security
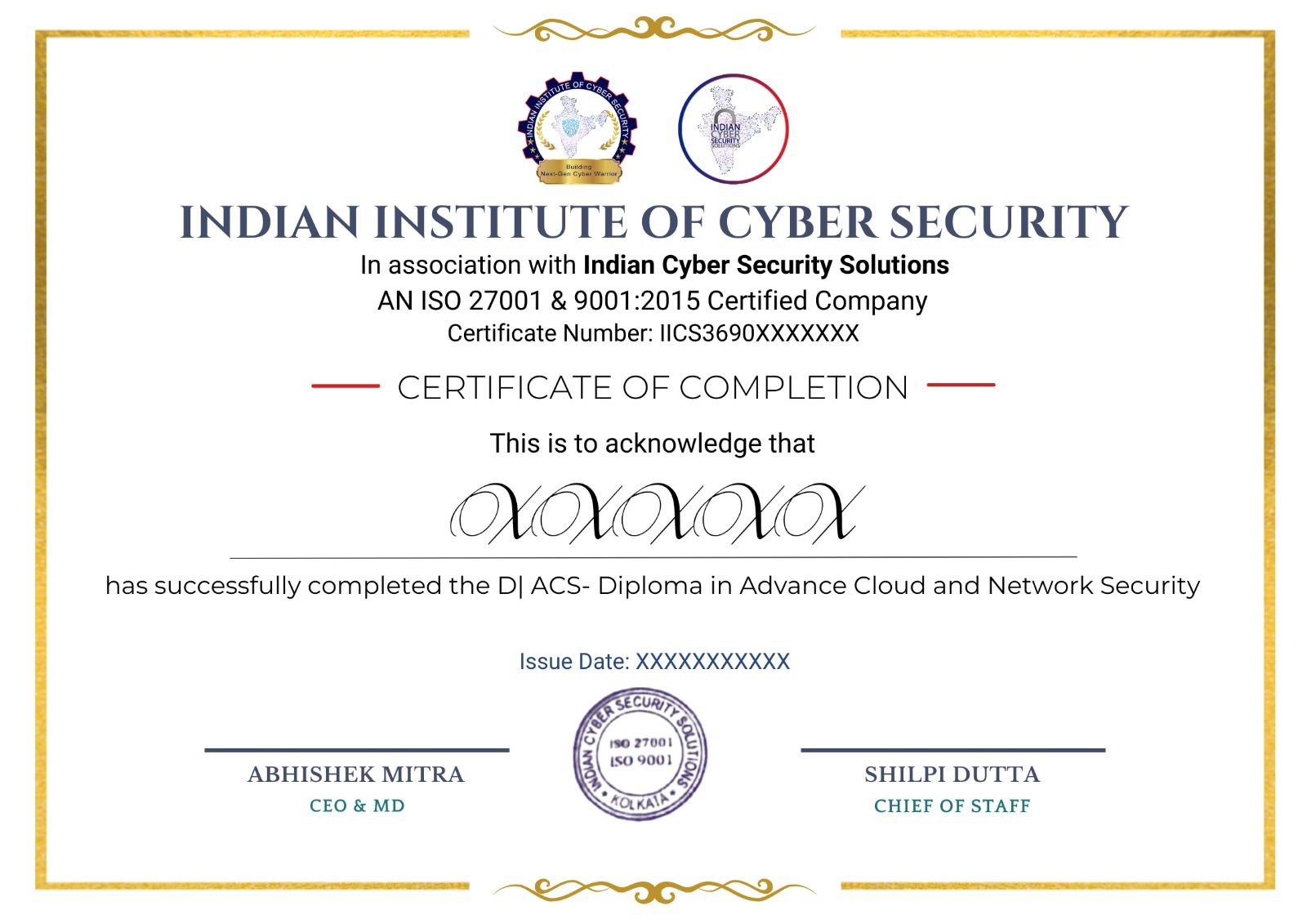
Diploma in Advanced Cloud & Network Security in India
2024 Ongoing Campus Placement
Indian Cyber Security Solutions (ICSS) stands out as the premier Diploma in Advanced Cloud & Network Security Institute in Kolkata. Strategically positioned in the heart of the city, our office is easily accessible, ensuring seamless connectivity for students from all parts of Kolkata. Located in Sector V, the IT hub of Kolkata, ICSS offers unparalleled advantages for aspiring cybersecurity professionals.
Sector V is renowned for its thriving tech ecosystem, hosting numerous IT companies and startups. This vibrant environment translates to increased on-campus placement drives, providing our students with direct access to potential employers. The supporting emails from companies participating in our campus recruitment programs testify to the success of our placement initiatives.
For students, finding affordable accommodation is hassle-free. Our institute is conveniently located at College More in Sector V, surrounded by numerous budget-friendly housing options. This proximity not only reduces commute time but also enhances the overall learning experience by fostering a conducive living and studying environment.
Our Diploma in Advanced Cloud & Network Security in India is designed to meet the highest industry standards, ensuring that students are well-equipped with the skills and knowledge demanded by employers. The comprehensive curriculum covers critical areas such as ethical hacking, network security, and incident response, making our graduates highly sought after in the job market.
Join ICSS and take the first step towards a successful career in cybersecurity. Experience the benefits of studying in Kolkata’s prime IT location, with ample placement opportunities and affordable living options. Transform your career with our Cyber Security Training and become a part of the elite group of cybersecurity professionals.
Since 2016, Indian Cyber Security Solutions (ICSS) has become the leading Diploma in Diploma in Advanced Cloud & Network Security Institute in Kolkata. Our program is designed to equip students with the skills needed to excel in the cybersecurity field. With a strong emphasis on practical, hands-on training, our graduates are well-prepared for the challenges of the industry.
ICSS boasts a stellar placement record, with students securing positions in prestigious companies like Wipro, TCS, and Amazon. Located in Sector V, Kolkata's IT hub, we provide students with excellent opportunities for networking and on-campus recruitment.
Our success over the years is a testament to our commitment to quality education and student success. Join ICSS and become part of a legacy of excellence in cybersecurity training. Enroll in our Diploma in Diploma in Advanced Cloud & Network Security Institute in Kolkata today and take the first step towards a promising career. Visit our website to learn more and register now!