Types of Penetration Testing Tools - Indian Cyber Security Solutions
Penetration testing (or pentesting) is a simulated cyber attack where professional ethical hackers break into corporate networks to find weaknesses of the system before attackers of the outsiders do. There are various Types of Penetration Testing Tools for Ethical Hackers to use as well as to test on devices as well as infrastructure of the organisation. With this, there are also various Penetration Testing service providers that offers the Penetration Testing Services to check out what weakness does the system have so as to avoid any data breach from the system. They utilise various Types of Penetration Testing Tools for the work to be done. These penetration testing tools not only helps in checking out where the weakness is within the company's system, But also how to improve the network security.
Ethical Hacking and Penetration Testing are common terms popular in the field of Information Security for a long time. Increase in Cybercrimes and Hacking has created a great challenge for Security Experts and Analysts over the last decade. It's like popular war between Hackers and Security professionals.
So, let’s get started and understand in a very basic and easy way what Penetration Testing is: Penetration Testing, also called as Pen-testing is a process of testing the security weaknesses of applications or a network. In other words, we try to find out how secure our network, applications or systems are Pen testers, who also try to find out the chances or possibilities of our applications being hacked or attacked.
A person who is expertise or who is authorized to do a pen test tries to break into the application or network and then tries to find out all the security weaknesses and at the end drafts a report which shows the security weaknesses and also gives some recommendations on that. Once the vulnerabilities are patched, the Pen-tester again checks if the system is now secure or do we have some other security weaknesses left.
Types of Penetration Testing Tools
There are several Types of Penetration Testing Tools.
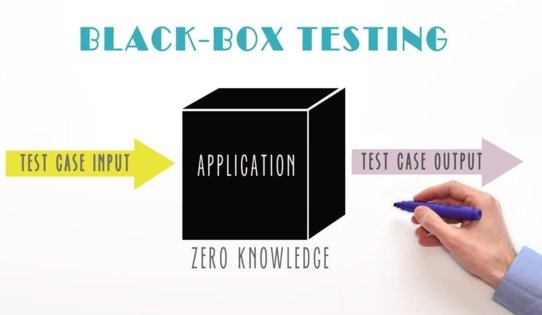
- Black Box Pen-Testing
Black Box Pen-testing, also known as External Testing, is where the external-facing assets of the company/ assets visible on the internet. These kinds of tests imitate a real-world attack where the tester does not know anything about the application/system/network.
The tester abstracts insights on the targets and evaluates their functionality based on inputs from automated processes or tools. The goal is to expose vulnerabilities that would not be detected otherwise.
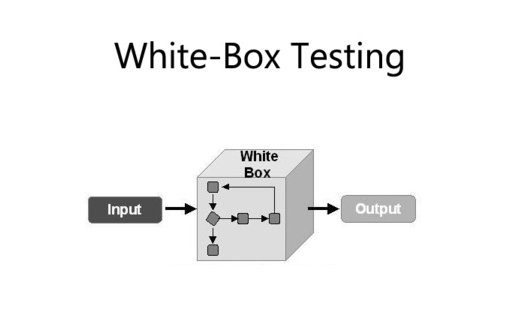
- White Box Pen-testing
White Box Pen-testing, also known as Internal Testing, is where the tester has root-/ admin-level access to and complete information (such as Source code, OS details, etc.) about the systems/ networks/ applications that are to be tested. The goal is to test the internal structure and strength of the systems/ networks/ applications against malicious insiders or an outsider who has stolen the credentials using a phishing attack.
The organizations provide the Pen-testers a variety of security information related to their systems to help them better find vulnerabilities.
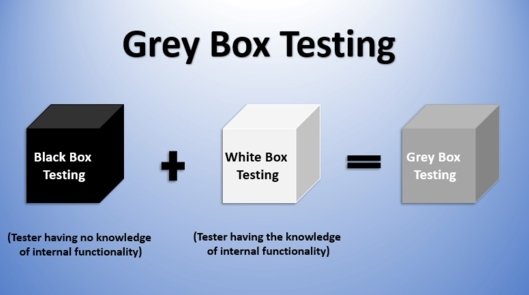
- Grey Box Pen-testing
Grey Box Pen-testing is where the tester is provided partial information about the systems/ networks/ applications such as access to software code, system architecture diagrams, etc. to simulate an attack. By obtaining only limited information, it is useful to help understand the level of access a privileged user could gain and the potential damage they could cause.
Phases of Penetration Testing
- Reconnaissance: Gathering information about the target before launching an attack using different tools and techniques.
- Scanning: Scanning is a pre-attack phase, where the attacker scans the network for identifying live hosts, ports and services, discovering OS and architecture of the target system, identifying threats and vulnerabilities in the network.
- Gaining access: In Gaining access, the hacker gets control over an Operating System, application or a computer network.
- Maintaining access: In this phase, the hacker tries to maintain the access, ownership and control over the compromised systems.
- Clearing Tracks: Clearing tracks is most required for an attacker to fulfil their intentions by continuing the access to the compromised system, remain undetected and gain what they want, remain unnoticed and wipe all evidence that indicates their identity.
- Reporting: In this phase, the attacker creates a report that includes all of these details, highlighting what was used to successfully penetrate the system, what security weaknesses were found, and any other pertinent information discovered. These reports should also include analysis to help map out next steps once the test has concluded.

Penetration Testing Service Providers
Since the Global Pandemic, there has been a rise in the demand of a proper professional Penetration Testing Professionals. We at Indian Cyber Security Solutions have been looking at Multi-National Companies demand and have been focusing to impart training and education knowledge to students who are interested in Penetration Testing. With Penetration Testing Service Providers in India by Indian Cyber Security Solutions, we enable an individual to become highly proficient in Ethical Hacking.
ICSS has secured 300+ website and web-based applications worldwide and gained considerable experience backed by qualified professions with certifications on CISSP, ISO-27001 Lead Auditor, and Certified Ethical Hacker. However, if you want to become a professional in the field of Penetration Testing, do join Indian Cyber Security Solutions. Although you know that there are many institutes that offer this training, Indian Cyber Security Solutions stands apart from these institutes due to our commitment in training students.

Also as an Education Institute, we provide Cyber Security Training to students as well and as many as One hundred thousand students have enrolled at the Indian Cyber Security Solutions, with many having pass the exams and becoming a cyber security professional.
With this we have been acknowledged as "One of the best Cyber Security Training Institute in India" by Silicon India, as well as the "Top 20 Tech Brands of 2021 in India" by Business Connect. Our achievements not only ends here, as we have added another feather to our institute as "10 Best Security Solutions Provider" by Industry Era. With our achievements, we strive to work hard more to impart the right cyber security knowledge to students so as to improve the cyber security infrastructure of our society.
DOES THIS ARTICLE HELPED YOU?
Stay updated and connected with Indian Cyber Security Solutions. Follow our social Medias (Facebook, Instagram, LinkedIn, YouTube) to get all updated and latest technology related news. We are the largest cybersecurity training & service provider in India. For any query feel free to contact us at 1800-123-500014 or write us at info@indiancybersecuritysolutions.com