Ransomware
Lets us see the pros and cons of both. And know about Ransomware in web applications
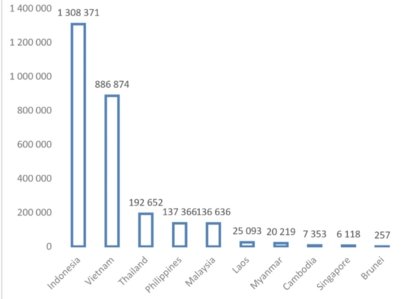
Ransomware is a significant threat in the ASIAN region. According to statistics provided by Kaspersky, there were about 2.7 million ransomware detections in ASIAN during the first three quarters of 2020. Among the ten ASIAN member countries, Indonesia suffered the most with 1.3 million counts, accounting for almost half of the entire detections in the region.
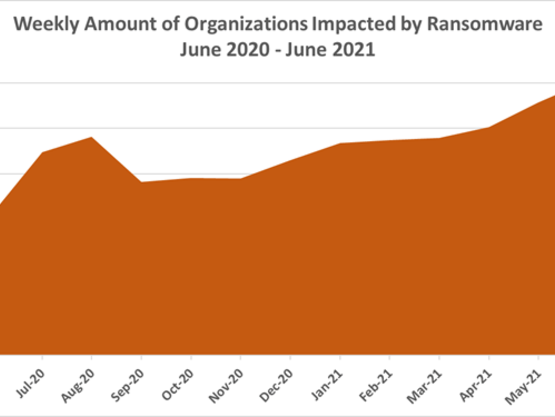
According to a study conducted by the Identity Theft Resource Center (ITRC), the average ransomware payouts for all businesses have grown from less than USD 10 000 in the third quarter of 2018 to more than USD 178 000 per event by the end of the second quarter of 2020. Large enterprises are making average ransomware payments of over USD 1 million. The sheer amount of returns is the main reason why the trend in ransomware is continuously on the rise.

According to Group-IB’s conservative estimates, the total financial damage from ransomware operations amounted to over USD 1 billion (USD 1 005 186 000), but the actual damage is likely to be much higher. It is also believed that the actual situation is worse as many individuals and businesses are unwilling to report cases to the police, with Group-IB estimating that only 2.5 per cent of ransomware incidents are made public.
The reasons for not reporting a ransomware attack can be the result of the lack of quantifiable value that an individual places in the data that have been encrypted, that may extend to a far more serious and worrying idea that businesses may not want their customers to know that their data have been compromised. Victims often remain silent about incidents and pay ransoms quietly, while attackers do not always publish data from compromised networks.
Further reports from Group-IB revealed that the top five most frequently attacked industries included manufacturing, retail, government agencies, healthcare, and construction. From similar reports, it is observed that other critical infrastructures, including energy sectors, are not spared. Particularly in 2020 during the COVID-19 pandemic, it has been observed that hospitals, medical centres and public institutions targeted by cybercriminals for ransomware attacks increased rapidly. Cybercriminals believe these institutions are more likely to pay the ransom because they are overwhelmed by the health crisis and cannot afford to be locked out of their systems. Within the ASEAN region, hospitals in Indonesia and Thailand have fallen victims. The amount of ransom demanded by the threat actors varies greatly and this can be attributed to two tactics used to distribute ransomware. The first is the spray-and-pray tactic where malware is distributed via mail spam or fake malicious advertisements, targeting anyone unfortunate enough to become a victim. The second tactic is the targeted tactic where the threat actors select their targets before actively looking for ways to infiltrate their network. Once the network has been mapped, the threat actors proceed to encrypt the data. The latter requires far more time and resources to carry out, and consequently, the amount of ransom demanded is higher.
The challenges of addressing ransomware attacks are numerous. Given the organized and now experienced nature of the attackers, the techniques and tactics used to avoid identification have advanced. While an attacker can make multiple attempts to infiltrate a network, it only takes a single mistake by a user – such as opening an e-mail attachment – for an attack to be successful. The organized schemes used by attackers prove how much information cybercriminals have about companies’ financial situations. Ransomware demands are carefully calibrated to appear as more financially viable options than the cost of restoring backups and the reputational damage to the company.
According to research conducted by Group-IB, Maze and REvil are considered to have the largest appetite: the operators of these two strains are believed to be behind more than half of all successful attacks. Ryuk, NetWalker, and DoppelPaymer come second. To compound the problem of ransomware, the “name and shame” tactic is used against infected companies. Hackers publicize corporate data for non-paying companies and even auction them for a higher profit. The Maze ransomware group is the only known group to use the “name and shame” tactic. However, it can be assumed that it is only a matter of time before this tactic becomes more widespread and targets businesses that operate in the ASEAN region.